Lesson Contents
OSPFv3 doesn’t have an authentication field in its header like OSPFv2 does, instead it relies on IPsec to get the job done.
IPsec supports two encapsulation types. The first one is AH (Authentication Header) which as the name implies, authenticates the header. The other encapsulation type is ESP (Encapsulating Security Payload) which encrypts packets. We can use both for OSPFv3 so besides authentication, encryption is also a possibility.
In this lesson I’ll show you how to configure both options.
Configuration
We will use the following topology for this:
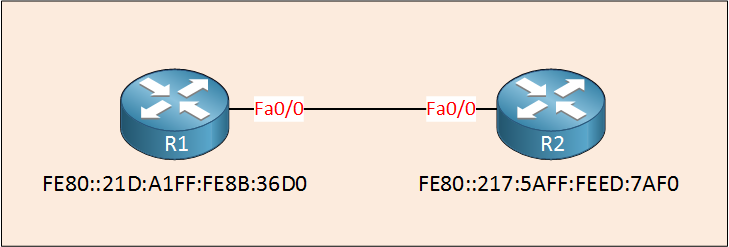
We only need two routers for this demonstration. I will only use the link-local IPv6 addresses on these two routers. Let’s enable OSPFv3:
R1 & R2#
(config)#interface FastEthernet 0/0
(config-if)#ipv6 ospf 1 area 0Now we can play with authentication…
IPsec Authentication
To get started we have to use the ipv6 ospf authentication command:
R1(config)#interface FastEthernet 0/0
R1(config-if)#ipv6 ospf authentication ?
ipsec Use IPsec authentication
null Use no authenticationSince we want authentication, we’ll select ipsec:
R1(config-if)#ipv6 ospf authentication ipsec ?
spi Set the SPI (Security Parameters Index)First we have to choose a SPI. You can pick any number you like but it has to match on both routers. Let’s pick the lowest available number (256):
R1(config-if)#ipv6 ospf authentication ipsec spi 256 ?
md5 Use MD5 authentication
sha1 Use SHA-1 authenticationNow we can choose what authentication we would like, MD5 or SHA1. SHA1 is more secure so let’s select that:
R1(config-if)#ipv6 ospf authentication ipsec spi 256 sha1 ?
0 The key is not encrypted (plain text)
7 The key is encrypted
Hex-string SHA-1 key (40 chars)Now we have to type in a key string ourselves. Normally IPsec uses IKE (Internet Key Exchange) for the security association between two devices. However since we can have multiple OSPFv3 neighbors on a single segment we can’t use IKE and we’ll have to use a static key instead.
For this example I will use an online SHA1 generator to generate a key but for a production network you really should use a safer method to generate a key. Let’s enter that key:
R1(config)#interface FastEthernet 0/0
R1(config-if)#ipv6 ospf authentication ipsec spi 256 sha1 A5DEC4DD155A695A8B983AACEAA5A97C6AECB6D1As soon as you do this the OSPFv3 neighbor adjacency will drop so let’s copy and paste the same line on R2:
R2(config)#interface FastEthernet 0/0
R2(config-if)#ipv6 ospf authentication ipsec spi 256 sha1 A5DEC4DD155A695A8B983AACEAA5A97C6AECB6D1That should do the job.
let’s verify our work:
R1#show ipv6 ospf interface FastEthernet 0/0 | include auth
SHA-1 authentication SPI 256, secure socket UP (errors: 0)R2#show ipv6 ospf interface FastEthernet 0/0 | include auth
SHA-1 authentication SPI 256, secure socket UP (errors: 0)If you look at the OSPF specific information on the interface then you can see that authentication has been enabled. Since we are using IPsec, you can also check the security associations:
R1#show crypto ipsec sa
interface: FastEthernet0/0
Crypto map tag: (none), local addr ::
IPsecv6 policy name: OSPFv3-1-256
IPsecv6-created ACL name: FastEthernet0/0-ipsecv6-ACL
protected vrf: (none)
local ident (addr/mask/prot/port): (FE80::/10/89/0)
remote ident (addr/mask/prot/port): (::/0/89/0)
current_peer :: port 500
PERMIT, flags={origin_is_acl,}
#pkts encaps: 50, #pkts encrypt: 50, #pkts digest: 50
#pkts decaps: 31, #pkts decrypt: 31, #pkts verify: 31
#pkts compressed: 0, #pkts decompressed: 0
#pkts not compressed: 0, #pkts compr. failed: 0
#pkts not decompressed: 0, #pkts decompress failed: 0
#send errors 0, #recv errors 0
local crypto endpt.: ::,
remote crypto endpt.: ::
path mtu 1500, ipv6 mtu 1500, ipv6 mtu idb FastEthernet0/0
current outbound spi: 0x100(256)
PFS (Y/N): N, DH group: none
inbound esp sas:
inbound ah sas:
spi: 0x100(256)
transform: ah-sha-hmac ,
in use settings ={Transport, }
conn id: 2001, flow_id: NETGX:1, sibling_flags 80000001, crypto map: (none)
no sa timing
replay detection support: N
Status: ACTIVE
inbound pcp sas:
outbound esp sas:
outbound ah sas:
spi: 0x100(256)
transform: ah-sha-hmac ,
in use settings ={Transport, }
conn id: 2002, flow_id: NETGX:2, sibling_flags 80000001, crypto map: (none)
no sa timing
replay detection support: N
Status: ACTIVE
outbound pcp sas:Above you can see our SPI number and that we are using SHA authentication. There’s one more useful command:
R1#show crypto ipsec policy
Crypto IPsec client security policy data
Policy name: OSPFv3-1-256
Policy refcount: 1
Inbound AH SPI: 256 (0x100)
Outbound AH SPI: 256 (0x100)
Inbound AH Key: A5DEC4DD155A695A8B983AACEAA5A97C6AECB6D1
Outbound AH Key: A5DEC4DD155A695A8B983AACEAA5A97C6AECB6D1
Transform set: ah-sha-hmacThis gives us a nice overview with our authentication method, SPI and keys. If you are interested, here’s a wireshark capture of our authenticated OSPFv3 packets:
Frame 5: 100 bytes on wire (800 bits), 100 bytes captured (800 bits)
Raw packet data
Internet Protocol Version 6, Src: fe80::21d:a1ff:fe8b:36d0 (fe80::21d:a1ff:fe8b:36d0), Dst: ff02::5 (ff02::5)
0110 .... = Version: 6
.... 1110 0000 .... .... .... .... .... = Traffic class: 0x000000e0
.... .... .... 0000 0000 0000 0000 0000 = Flowlabel: 0x00000000
Payload length: 60
Next Header: Authentication Header (51)
Hop limit: 1
Source: fe80::21d:a1ff:fe8b:36d0 (fe80::21d:a1ff:fe8b:36d0)
[Source SA MAC: Cisco_8b:36:d0 (00:1d:a1:8b:36:d0)]
Destination: ff02::5 (ff02::5)
[Source GeoIP: Unknown]
[Destination GeoIP: Unknown]
Authentication Header
Next Header: OSPF IGP (0x59)
Length: 24
AH SPI: 0x00000100
AH Sequence: 37
AH ICV: ab40a9a153af39447418edcd
Open Shortest Path First
OSPF Header
Version: 3
Message Type: Hello Packet (1)
Packet Length: 36
Source OSPF Router: 1.1.1.1 (1.1.1.1)
Area ID: 0.0.0.0 (0.0.0.0) (Backbone)
Checksum: 0x2212 [correct]
Instance ID: IPV6 unicast AF (0)
Reserved: 00
OSPF Hello Packet
Interface ID: 3
Router Priority: 1
Options: 0x000013 (R, E, V6)
Hello Interval [sec]: 10
Router Dead Interval [sec]: 40
Designated Router: 0.0.0.0 (0.0.0.0)
Backup Designated Router: 0.0.0.0 (0.0.0.0)Above you can see the authentication header. If you want to take a look for yourself then you can find the capture file here.
Configurations
Want to take a look for yourself? Here you will find the final configuration of each device.
R1
hostname R1
!
ipv6 unicast-routing
!
interface fastEthernet 0/0
ipv6 enable
ipv6 ospf 1 area 0
ipv6 ospf authentication ipsec spi 256 sha1 A5DEC4DD155A695A8B983AACEAA5A97C6AECB6D1
!
ipv6 router ospf 1
router-id 1.1.1.1
!
endR2
hostname R2
!
ipv6 unicast-routing
!
interface fastEthernet 0/0
ipv6 enable
ipv6 ospf 1 area 0
ipv6 ospf authentication ipsec spi 256 sha1 A5DEC4DD155A695A8B983AACEAA5A97C6AECB6D1
!
ipv6 router ospf 1
router-id 2.2.2.2
!
endIPsec Encryption
Let’s take a look at the second method, using IPsec ESP to authenticate and encrypt OSPFv3 traffic. Let’s get rid of the current IPsec AH configuration:
R1 & R2#
(config)#interface FastEthernet 0/0
(config-if)no ipv6 ospf authentication ipsec spi 256 sha1 A5DEC4DD155A695A8B983AACEAA5A97C6AECB6D1Now we can enable ESP, there’s a different command we have to use:


Rene, do you have IPSEC lesson?
Hi John,
I just published it, it’s a long story:
https://networklessons.com/security/ipsec-internet-protocol-security
Let me know what you think of it.
Rene
Is the “0” or “7” option relating to whether or not the running-config file saves the key as encrypted or clear text?
Hello Chris
Options 0 and 7 refer to whether or not the key that is sent between the routers during the authentication process is encrypted. In order to encrypt the key in the configuration file, use the
system password-encryptioncommand. This command encrypts authentication key passwords among others.I hope this has been helpful!
Laz
Hi,
does this means IPsec is the only way to authenticate in OSPFv3?
I tried with the following and it worked:
thanks
Edit: This post gives the idea that OSPFv3 does not support any authentication beside IPsec, but after checking it does support t
... Continue reading in our forum