The spanning tree BPDU filter works similarly to BPDU Guard as it allows you to block malicious BPDUs. The difference is that BPDUguard will put the interface that receives the BPDU on in err-disable mode while BPDU filter just “filters” it. In this lesson, we’ll take a good look at how the BPDU filter works.
BPDU filter can be configured globally or on the interface level, and there’s a difference:
- Global: if you enable BPDU filter globally then any interface with portfast enabled will not send or receive any BPDUs. When you receive a BPDU on a portfast-enabled interface it will lose its portfast status, disables BPDU filtering, and acts as a normal interface.
- Interface: if you enable BPDU filter on the interface it will ignore incoming BPDUs, and it will not send any BPDUs. This is the equivalent of disabling spanning tree.
You have to be careful when you enable BPDU filter on interfaces. You can use it on interfaces in access mode that connect to computers but make sure you never configure it on interfaces connected to other switches; if you do you might end up with a loop.
Configuration
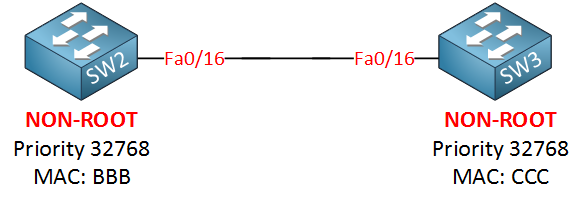
Let’s use the following topology to demonstrate the BPDU filter:
Let’s enable portfast on SW2’s interface and enable BPDU filter:
SW2(config)#interface fa0/16
SW2(config-if)#spanning-tree portfast trunk
SW2(config-if)#spanning-tree bpdufilter enableIt will stop sending BPDUs, and it will ignore whatever is received. Let’s enable a debug to see what it does:


Hi Rene,
Do you know what exactly happens when BPDU filter and Guard are both enabled on aportfast enabled interface and then a BPDU’s are suddenly received? I cannot find a clear answer on that anywhere. I read that BPDU filter takes precedence over BPDU guard when both configured on the interface, but it is still unclear to me what happens when in this case bpdu’s are received on a port configured this way.
Hi Edwin,
I just labbed this up. When you enable BPDU filter & guard at the same time then filter takes precedence. The BPDUs are ignored, the interface doesn’t go in err-disabled because of BPDUguard anymore.
Rene
Thanks Rene!
That thus confirms that the guard fuction is useless when both guard and filter are enabled on the interface, as the guard never kicks in due to the bpdu’s being filtered beforehand
Yup that’s right
Hi Rene,
Configuring command “spanning-tree portfast trunk” for trunk port is needed ?.
“spanning-tree bpdufilter enable” command anything to do with the above command.
Thanks,
SV