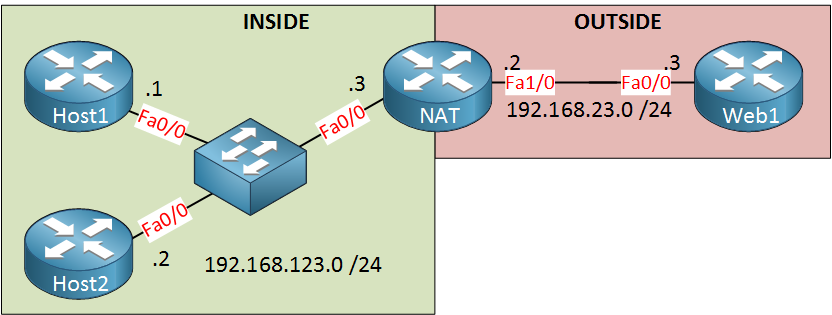
I have covered the configuration of static NAT and dynamic NAT in previous lessons, now it’s time for PAT. This is the topology we’ll use:
Let’s prepare the hosts. I am using normal Cisco routers with ip routing disabled to turn them into dumb hosts:
Host1(config)#no ip routing
Host1(config)#ip default gateway 192.168.123.3Host2(config)#no ip routing
Host2(config)#ip default-gateway 192.168.123.3The next step is to configure NAT:
NAT(config)#interface fastEthernet 0/0
NAT(config-if)#ip nat inside NAT(config)#interface fastEthernet 1/0
NAT(config-if)#ip nat outsideSo far so good. Let’s create an access-list that matches both hosts:
NAT(config)#access-list 1 permit 192.168.123.0 0.0.0.255And finally, we’ll configure PAT:
NAT(config)#ip nat inside source list 1 interface fastEthernet 1/0 overloadI select access-list 1 as my inside source, and I will translate them to the IP address on FastEthernet 1/0. The big magic keyword here is overload. If you add this, we will enable PAT!
Let’s give it a test run, shall we?



tyvm Sir Rene …
#ip nat inside source list 1 interface fastEthernet 1/0 overload
I do not know which interface fa1/0 meant.
Can you please describe more specifically.
N#interface fastEthernet 0/0
Are you sure the interface is correct Sir?
Please shed some light.
I will take CCNA in this month.
on the NAT router, there are 2 fastethernet1/0 (inside and outside)
Hi Ted,
I just changed the picture so the fastethernet interface match with the configs. It should make more sense now.
Rene