GLBP stands for Gateway Load Balancing Protocol, and just like HSRP / VRRP, it is used to create a virtual gateway that you can use for hosts. If you have no idea what a virtual gateway is, then read my Introduction to Gateway Redundancy first. Also, I would recommend looking at the HSRPand VRRP lessons before you continue with GLBP.
One of the key differences of GLBP is that it can do load balancing without the group configuration that HSRP/VRRP use.
Let’s take a closer look:
All devices running GLBP elect an AVG (Active Virtual Gateway). There will be only one AVG for a single group running GLBP, but other devices can take over this rule if the AVG fails. The role of the AVG is to assign a virtual MAC address to all other devices running GLBP. All devices will become an AVF (Active Virtual Forwarder), including the AVG. Whenever a computer sends an ARP Request, the AVG will respond with one of the virtual MAC addresses of the available AVFs. Because of this mechanism, all devices running GLBP will be used to forward IP packets.
There are multiple methods for load balancing:
- Round-robin: the AVG will hand out the virtual MAC address of AVF1, then AVF2, AVF3, and get back to AVF1, etc.
- Host-dependent: A host can use the same virtual MAC address of an AVF as long as it is reachable.
- Weighted: If you want some AVFs to forward more traffic than others, you can assign them a different weight.
Let’s take a look at a configuration example so you can see how this works.
Configuration
I will use the following topology to configure GLBP:
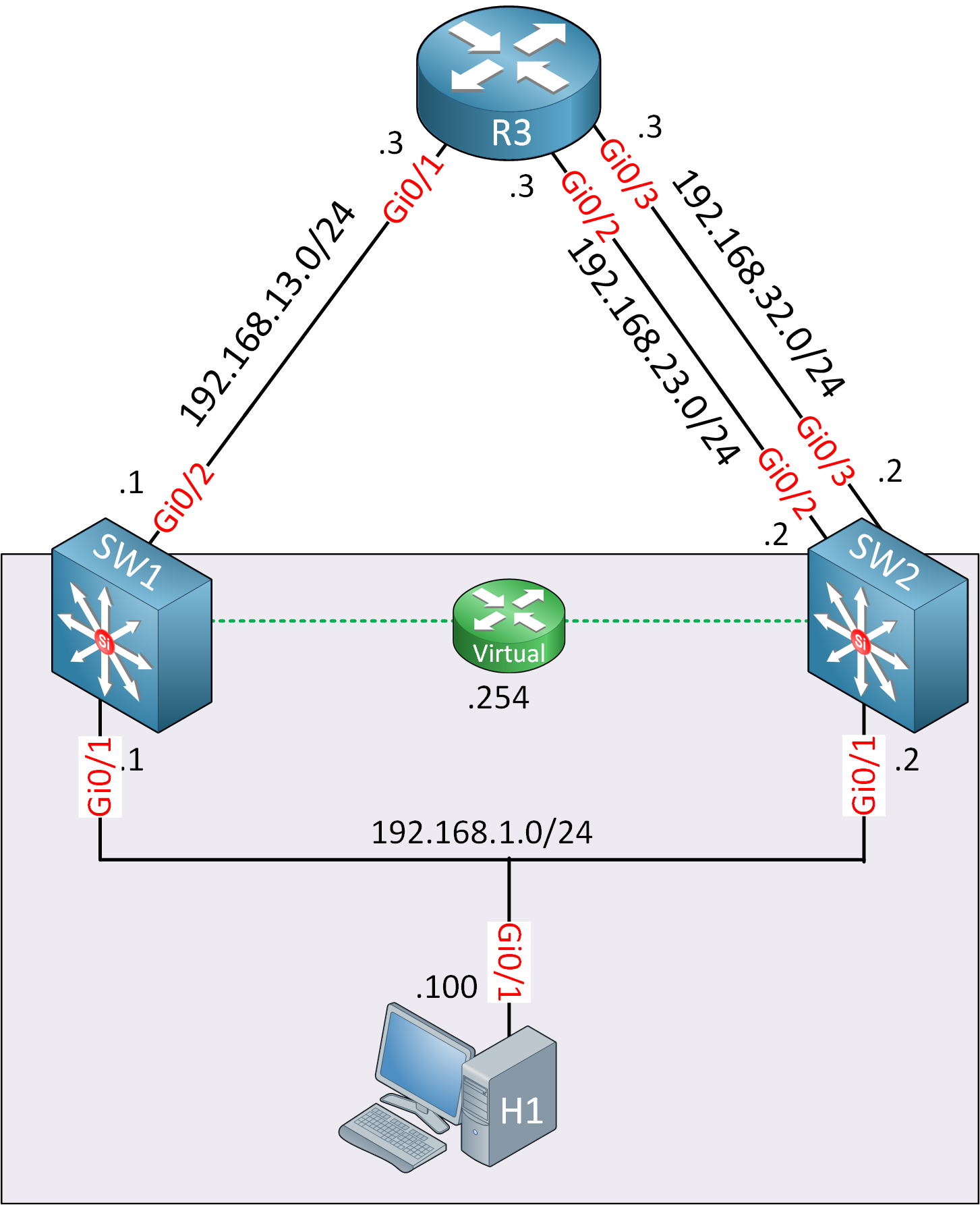
SW1 and SW2 are multilayer switches. Their GigabitEthernet 0/1 interfaces are switch ports and in VLAN 1. Their interfaces that connect to R3 are routed ports. We configure SW1 and SW2 so they create a virtual gateway for the hosts in the 192.168.1.0 /24 subnet. Let’s enable GLBP:
SW1(config)#interface Vlan1
SW1(config-if)#glbp 1 ip 192.168.1.254
SW1(config-if)#glbp 1 priority 150SW2(config)#interface Vlan1
SW2(config-if)#glbp 1 ip 192.168.1.254I’ll enable GLBP on SW1 and SW2 using the same group number (1). I changed the priority on SW1 because I want it to be the AVG. Let’s see if this works:
SW1#show glbp brief
Interface Grp Fwd Pri State Address Active router Standby router
Vl1 1 - 150 Active 192.168.1.254 local 192.168.1.2
Vl1 1 1 - Active 0007.b400.0101 local -
Vl1 1 2 - Listen 0007.b400.0102 192.168.1.2 -SW2#show glbp brief
Interface Grp Fwd Pri State Address Active router Standby router
Vl1 1 - 100 Standby 192.168.1.254 192.168.1.1 local
Vl1 1 1 - Listen 0007.b400.0101 192.168.1.1 -
Vl1 1 2 - Active 0007.b400.0102 local -Use the show glbp brief command to verify your configuration. There are a couple of things we can see here:
• SW1 has become the AVG for group 1. SW2 (192.168.1.2) is standby for the AVG role and will take over in case SW1 fails. Group1 has two AVFs:
- 1: SW1: Virtual MAC address 0007.b400.0101.
- 2: SW2: Virtual MAC address 0007.b400.0102.
The virtual MAC address that GLBP uses is 0007.b400.XXYY (where X = GLBP group number and Y = AVF number). Let’s take a look at our host. I configured it to use the 192.168.1.254 address for the default gateway.


great
Hi Rene,
How many AVFs supported by GLBP?
From the GLBP Virtual mac address 0007.b400.XXYY , I can found 256 Group , and 256 AVF.
Is it supports 256 AVF?
Thanks,
Srini
Hi Srini,
I think it depends on the hardware platform. I just took a look around and the supervisor 720 supports up to 1024 groups.
Rene
where do i choose an ip address from ? I want to implement GLBP between 2 core routers -
BGP router ( ISP )
Core router ____GLBP ______Core router
Layer 3 switch
Fire wall
Layer 3 switch ( access level , supporting VLANS ) subnet 126.89.120.0/27
Hi Aaron,
GLBP is configured for each subnet so if you want redundancy within the VLAN that has subnet 126.89.120.0/27 then that’s where you’ll need to pick an IP address from.
Rene