Lesson Contents
When your router learns about a prefix through EBGP and an IGP (RIP, OSPF or EIGRP) then it will always prefer the external BGP route. EBGP uses an administrative distance of 20 so it’s preferred over OSPF (110), RIP (120), or EIGRP (90).
This can introduce a problem, let me show you a scenario:
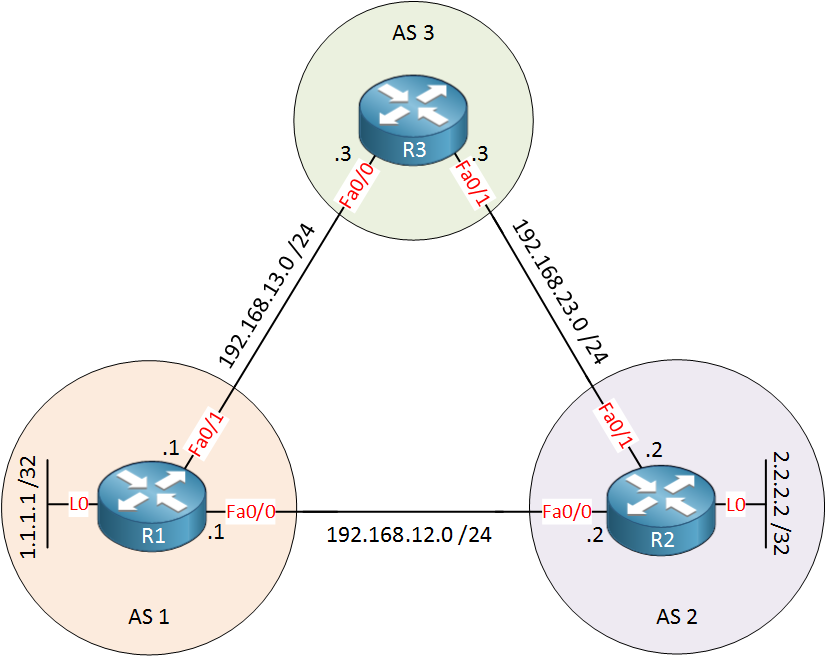
Above you see 3 routers, R1, R2, and R3. Imagine R1 and R2 are two sites from a customer, and R3 is the ISP router.
R1 and R2 have a fast “backdoor” link, and OSPF is configured to exchange some prefixes between the two sites. To illustrate this, I have added a loopback interface on these two routers.
R1 and R2 are also configured to use EBGP with R3, they advertise the same prefixes as they do in OSPF. This introduces a problem:
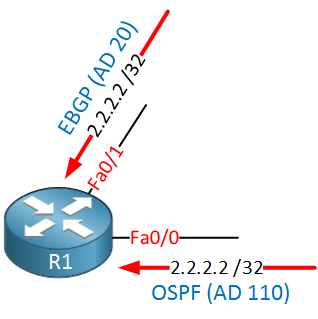
Above you see that R1 learns about the 2.2.2.2 /32 prefix through BGP (R3) and OSPF (R2). Since EBGP has a lower (thus better) AD, it will install this path in its routing table. The same thing applies to R2 for the 1.1.1.1 /32 prefix.
Let’s take a look at this scenario on our routers, I’ll configure OSPF and BGP, and you will learn how to fix this problem.
OSPF Configuration
First, we’ll configure R1 and R2 to run OSPF. I’ll advertise their loopback interfaces:
R1(config)#router ospf 1
R1(config-router)#network 192.168.12.0 0.0.0.255 area 0
R1(config-router)#network 1.1.1.1 0.0.0.0 area 0R2(config)#router ospf 1
R2(config-router)#network 192.168.12.0 0.0.0.255 area 0
R2(config-router)#network 2.2.2.2 0.0.0.0 area 0Nothing special here, just a basic OSPF configuration. Here’s what the routing table of R1 and R2 looks like now:
R1#show ip route ospf | include 2.2
O 2.2.2.2 [110/2] via 192.168.12.2, 00:00:12, FastEthernet0/0R2#show ip route ospf | include 1.1
O 1.1.1.1 [110/2] via 192.168.12.1, 00:00:27, FastEthernet0/0They learned about each other’s prefixes, great! Our next move is configuring BGP…
BGP Configuration
R1 and R2 will both peer with R3, and I’ll advertise their loopback interfaces in BGP:
R1(config-router)#neighbor 192.168.13.3 remote-as 3
R1(config-router)#network 1.1.1.1 mask 255.255.255.255R2(config-router)#neighbor 192.168.23.3 remote-as 3
R2(config-router)#network 2.2.2.2 mask 255.255.255.255R3(config)#router bgp 3
R3(config-router)#neighbor 192.168.13.1 remote-as 1
R3(config-router)#neighbor 192.168.23.2 remote-as 2It’s just a plain and simple BGP configuration. Now look again at the routing table of R1 and R2:
R1#show ip route | incl 2.2
B 2.2.2.2 [20/0] via 192.168.13.3, 00:00:45R2#show ip route | incl 1.1
B 1.1.1.1 [20/0] via 192.168.23.3, 00:01:23R1 and R2 will now use R3 to reach each other’s loopback interfaces. This happens because the AD of EBGP is 20 while OSPF has an AD of 110. As a result, OSPF is removed from the routing table. So how do we fix this? You could change the administrative distance manually, but this lesson is about the “backdoor” feature, so let’s see how it works.
BGP Backdoor Configuration
We have to configure the network that we want to use our “backdoor” for. Here’s what it looks like:
R1(config-router)#network 2.2.2.2 mask 255.255.255.255 backdoorR2(config-router)#network 1.1.1.1 mask 255.255.255.255 backdoorYou use the network command but add the backdoor keyword at the end.
Verification
Let’s see what changed:
R1#show ip route | incl 2.2
O 2.2.2.2 [110/2] via 192.168.12.2, 00:00:42, FastEthernet0/0
R2#show ip route | incl 1.1
O 1.1.1.1 [110/2] via 192.168.12.1, 00:00:28, FastEthernet0/0Great! Our routers now prefer the OSPF routes again. The prefixes are still in BGP, as you can see here:
R1#show ip bgp
BGP table version is 7, local router ID is 1.1.1.1
Status codes: s suppressed, d damped, h history, * valid, > best, i - internal,
r RIB-failure, S Stale, m multipath, b backup-path, x best-external, f RT-Filter
Origin codes: i - IGP, e - EGP, ? - incomplete
Network Next Hop Metric LocPrf Weight Path
*> 1.1.1.1/32 0.0.0.0 0 32768 i
r> 2.2.2.2/32 192.168.13.3 0 3 2 iR2#show ip bgp
BGP table version is 7, local router ID is 2.2.2.2
Status codes: s suppressed, d damped, h history, * valid, > best, i - internal,
r RIB-failure, S Stale, m multipath, b backup-path, x best-external, f RT-Filter
Origin codes: i - IGP, e - EGP, ? - incomplete
Network Next Hop Metric LocPrf Weight Path
r> 1.1.1.1/32 192.168.23.3 0 3 1 i
*> 2.2.2.2/32 0.0.0.0 0 32768 iThis is a good thing. When the backdoor link fails, we can still use the information from BGP. Let’s simulate that:


excellent and very helpful note . easily to understand . for all u articles.. i’n new to your website but really i thanksfull for your great effort. .
Thanx a lot Rene … Excellent explanation … It was so systematic … to the point … and U made it so easy to understand … Great work
Great topic. Thanks Rene
Excellent! Thank you Rene! Can we assume that R1 and R2 are remote offices interconnected via L2 MPLS and the BGP peering is used for redundancy?
Hi Marty,
That could be possible yes. MPLS L3 VPN is also possible, perhaps a topology like this:
MPLS L3 VPN Configuration
Rene