The IEEE 802.1Q trunking protocol describes something called the native VLAN. All native VLAN traffic is untagged; it doesn’t have an 802.1Q tag on the Ethernet frame. When you look at it in Wireshark, it will look the same, just like any standard Ethernet frame.
When your Cisco switches receive an Ethernet frame without a tag on an 802.1Q-enabled interface, it will assume it belongs to the native VLAN. For this reason, you need to make sure that the native VLAN is the same on both sides.
By default, VLAN 1 is the native VLAN. We can change this if we want. Let’s look at an example. I will use two switches for this:
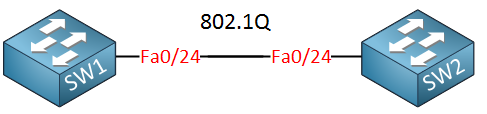
I will configure an 802.1Q trunk between those two switches so we can look at the native VLAN:
SW1(config)#interface Fastethernet 0/24
SW1(config-if)#switchport trunk encapsulation dot1q
SW1(config-if)#switchport mode trunkSW2(config)#interface Fastethernet 0/24
SW2(config-if)#switchport trunk encapsulation dot1q
SW2(config-if)#switchport mode trunkWe can verify our trunk configuration and see the native VLAN like this:
SW1#show interface fastEthernet 0/24 trunk
Port Mode Encapsulation Status Native vlan
Fa0/24 on 802.1q trunking 1
Port Vlans allowed on trunk
Fa0/24 1-4094
Port Vlans allowed and active in management domain
Fa0/24 1,10,12-13,20,23,34,100,123
Port Vlans in spanning tree forwarding state and not pruned
Fa0/24 1,10,12-13,20,23,34,100,123SW2#show interfaces fastEthernet 0/24 trunk
Port Mode Encapsulation Status Native vlan
Fa0/24 on 802.1q trunking 1
Port Vlans allowed on trunk
Fa0/24 1-4094
Port Vlans allowed and active in management domain
Fa0/24 1,10,12-13,20,23-24,30
Port Vlans in spanning tree forwarding state and not pruned
Fa0/24 1,10,12-13,20,23-24,30Above, you can see that the trunk is operational, we are using 802.1Q encapsulation, and the native VLAN is 1. So what kind of traffic is running on the native VLAN? Let’s take a look at a Wireshark capture of our trunk:
Frame 1: 606 bytes on wire (4848 bits), 606 bytes captured (4848 bits) on interface 0
IEEE 802.3 Ethernet
Destination: CDP/VTP/DTP/PAgP/UDLD (01:00:0c:cc:cc:cc)
Source: Cisco_0b:36:1a (00:11:bb:0b:36:1a)
Length: 592
Logical-Link Control
Cisco Discovery ProtocolAs you can see, some management protocols like CDP (Cisco Discovery Protocol) are sent on the native VLAN. For security reasons, it might be a good idea to change the native VLAN from VLAN 1 to something else. You can do it like this:
SW1(config)#interface fastEthernet 0/24
SW1(config-if)#switchport trunk native vlan 10SW2(config)#interface fastEthernet 0/24
SW2(config-if)#switchport trunk native vlan 10Instead of VLAN 1, we will now use VLAN 10 as the native VLAN. Let’s verify our work:
SW1#show interfaces fastEthernet 0/24 trunk
Port Mode Encapsulation Status Native vlan
Fa0/24 on 802.1q trunking 10SW2#show interfaces fastEthernet 0/24 trunk
Port Mode Encapsulation Status Native vlan
Fa0/24 on 802.1q trunking 10There we go. VLAN 10 is now the native VLAN. Last but not least, we can also configure our switches to tag the native VLAN just like any other VLAN. Here’s how to do it:
SW1(config)#vlan dot1q tag nativeSW2(config)#vlan dot1q tag nativeThat’s all there is to it! Hopefully, this lesson has been helpful to you in understanding the native VLAN and how to configure it.


Is there any specific reason to tag the native vlan?
Is there any specific reason to tag the native vlan?
Hi Dan,
There is a security vulnerability (VLAN Hopping) when you don’t tag the native VLAN, that’s the only reason I can think of.
If you are interested, I can do a write up for VLAN hopping…might be interesting
Rene
Thanks for your answer Rene, of course it would be interesting to have the write up for VLAN hopping
Regards
Hi Dan,
I put it on my list, when it’s done I’ll let you know.
Rene