Lesson Contents
We have installed Cisco SD-WAN controllers, onboarded vEdge routers, and learned how to use templates.
It’s about time we send traffic between sites. That’s what we can do with a service VPN. We can configure service VPNs from the CLI or with templates. I’ll show you both options in this lesson.
Configuration
This is the topology we have:
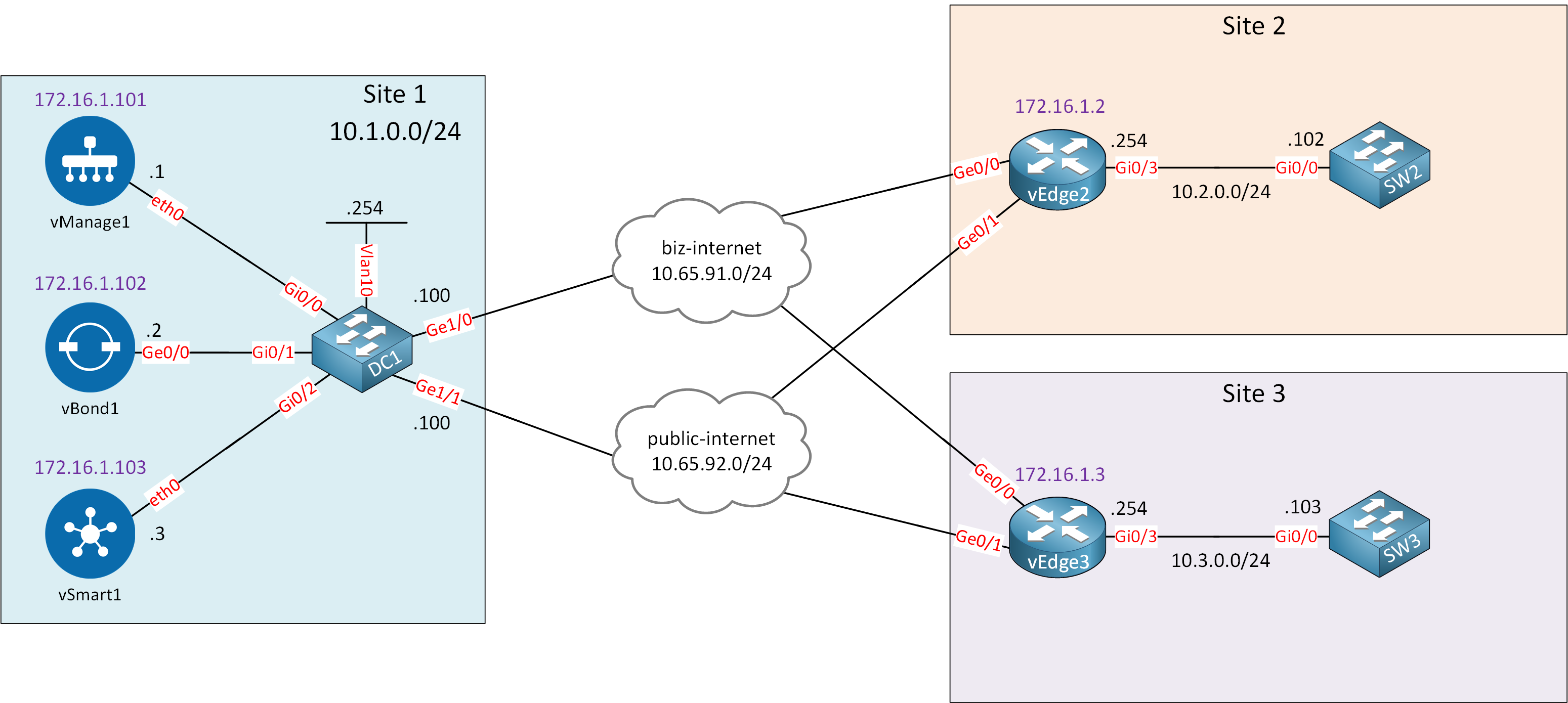
I have two vEdge devices, each on its own site. Behind each vEdge router is a switch. I’ll use these switches to ping from one site to another.
Configurations
Want to take a look for yourself? Here you will find the startup configuration of each device.
vEdge2
system
host-name vEdge2
system-ip 172.16.1.2
site-id 2
organization-name nwl-lab-sdwan
vbond 10.1.0.2
!
vpn 0
interface ge0/0
ip address 10.65.91.2/24
ipv6 dhcp-client
tunnel-interface
encapsulation ipsec
color biz-internet
allow-service all
!
no shutdown
!
interface ge0/1
ip address 10.65.92.2/24
tunnel-interface
encapsulation ipsec
color public-internet
allow-service all
!
no shutdown
!
ip route 10.1.0.0/24 10.65.91.100vEdge3
system
host-name vEdge3
system-ip 172.16.1.3
site-id 3
organization-name nwl-lab-sdwan
vbond 10.1.0.2
!
vpn 0
interface ge0/0
ip address 10.65.91.3/24
ipv6 dhcp-client
tunnel-interface
encapsulation ipsec
color biz-internet
allow-service all
!
no shutdown
!
interface ge0/1
ip address 10.65.92.3/24
tunnel-interface
encapsulation ipsec
color public-internet
allow-service all
!
no shutdown
!
ip route 10.1.0.0/24 10.65.91.100SW2
hostname SW2
!
no ip routing
!
interface GigabitEthernet0/0
no switchport
ip address 10.2.0.102 255.255.255.0
!
ip default-gateway 10.2.0.254SW3
hostname SW3
!
no ip routing
!
interface GigabitEthernet0/0
no switchport
ip address 10.3.0.103 255.255.255.0
!
ip default-gateway 10.3.0.254CLI
We’ll start with the CLI option.
Create a new VPN, assign the ge0/3 interface to it and configure an IP address:
vEdge2(config)# vpn 10
vEdge2(config-vpn-10)# interface ge0/3
vEdge2(config-interface-ge0/3)# ip address 10.2.0.254/24
vEdge2(config-interface-ge0/3)# no shutdown
vEdge2(config-interface-ge0/3)# commitvEdge3(config)# vpn 10
vEdge3(config-vpn-10)# interface ge0/3
vEdge3(config-interface-ge0/3)# ip address 10.3.0.254/24
vEdge3(config-interface-ge0/3)# no shutdown
vEdge3(config-interface-ge0/3)# commitThat’s all you have to configure. There aren’t any commands that you haven’t seen before. You can pick any VPN number except 0 or 512.
Templates
Now let’s see how we can configure a service VPN with templates.
Feature Templates
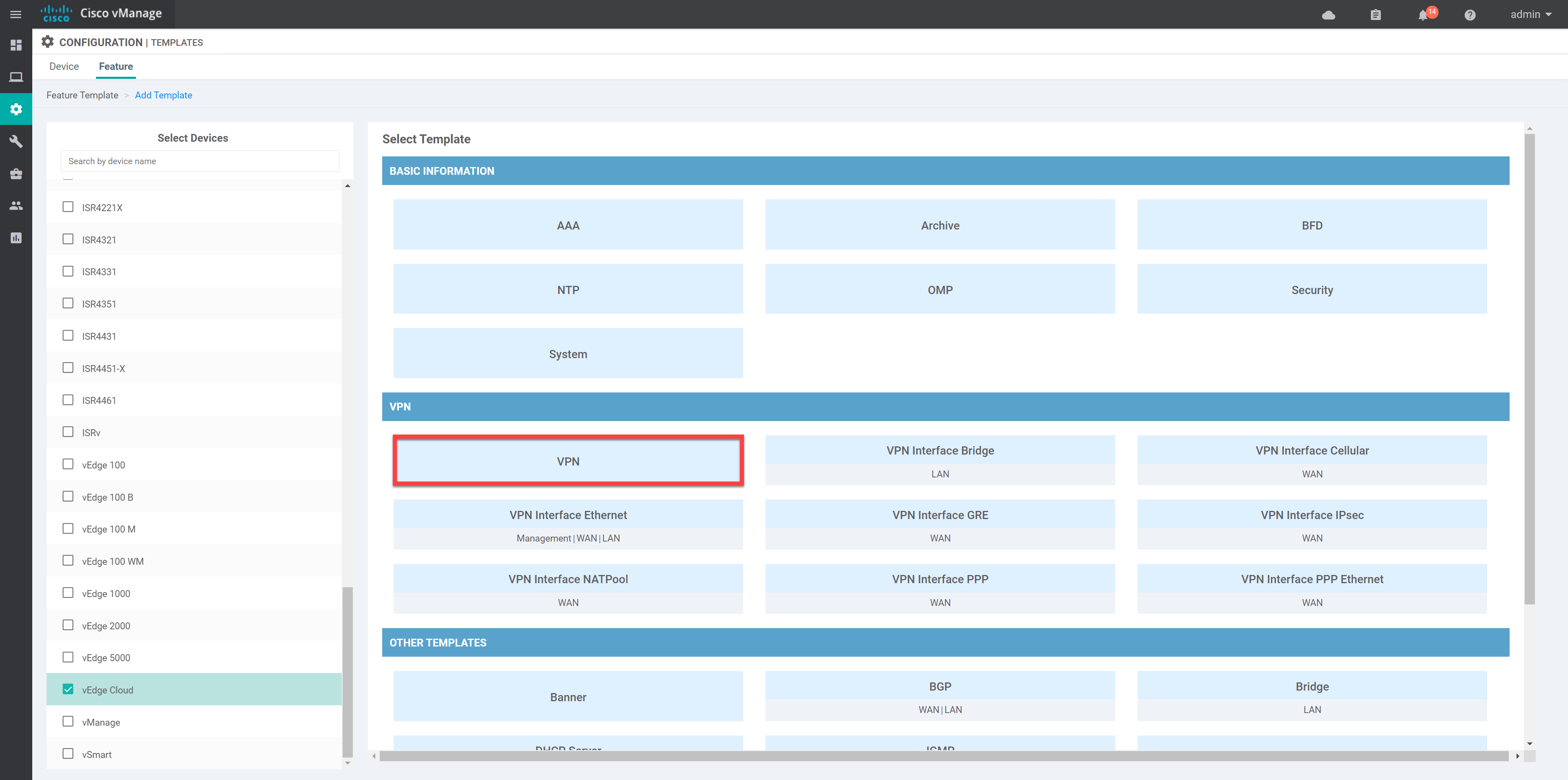
This takes some more work. Go to Configuration > Templates > Feature and click on Add Template.
VPN10
In the next screen, select the VPN feature template:
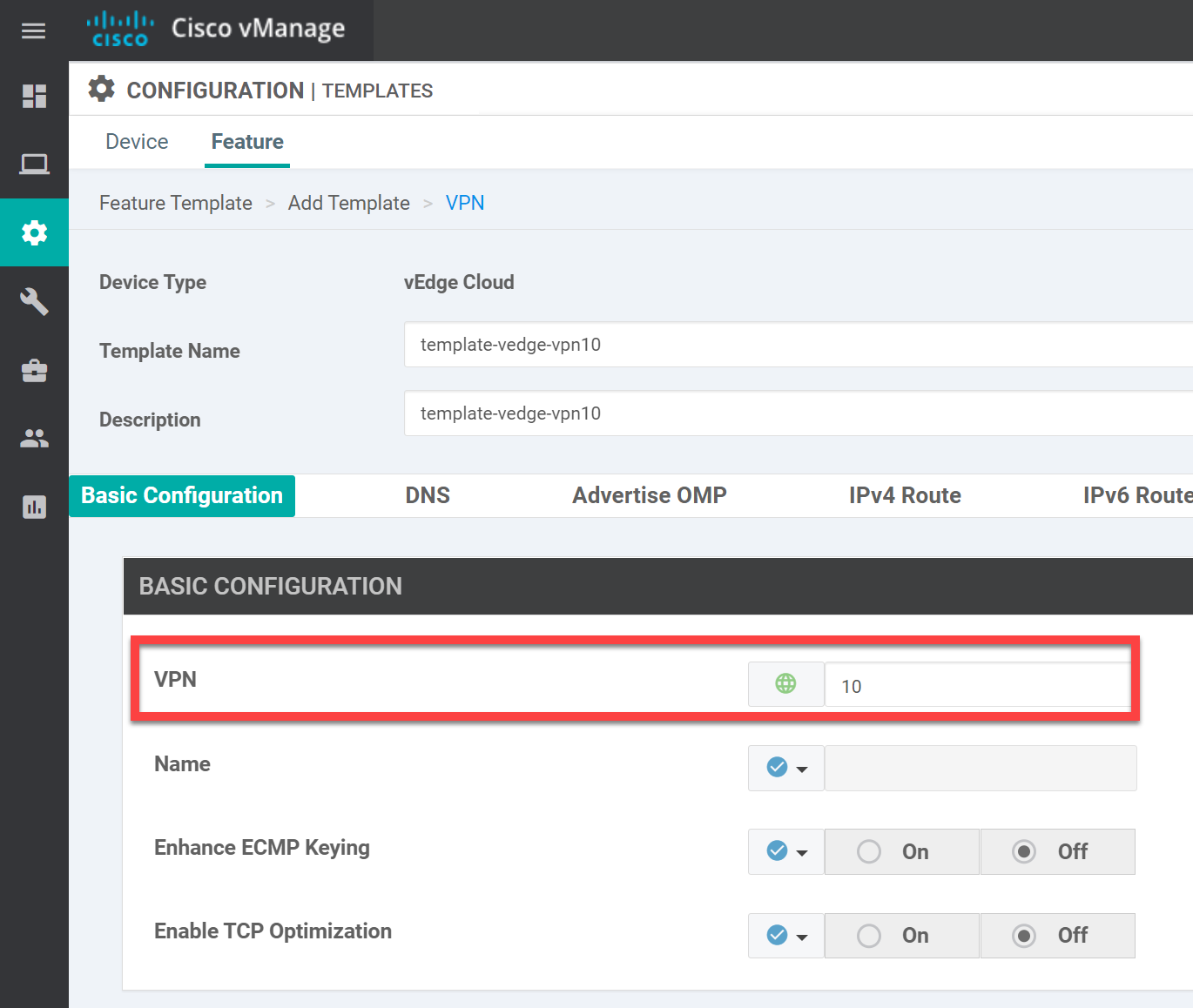
There are two items we need to change here. Under Basic Configuration, set the VPN to 10:
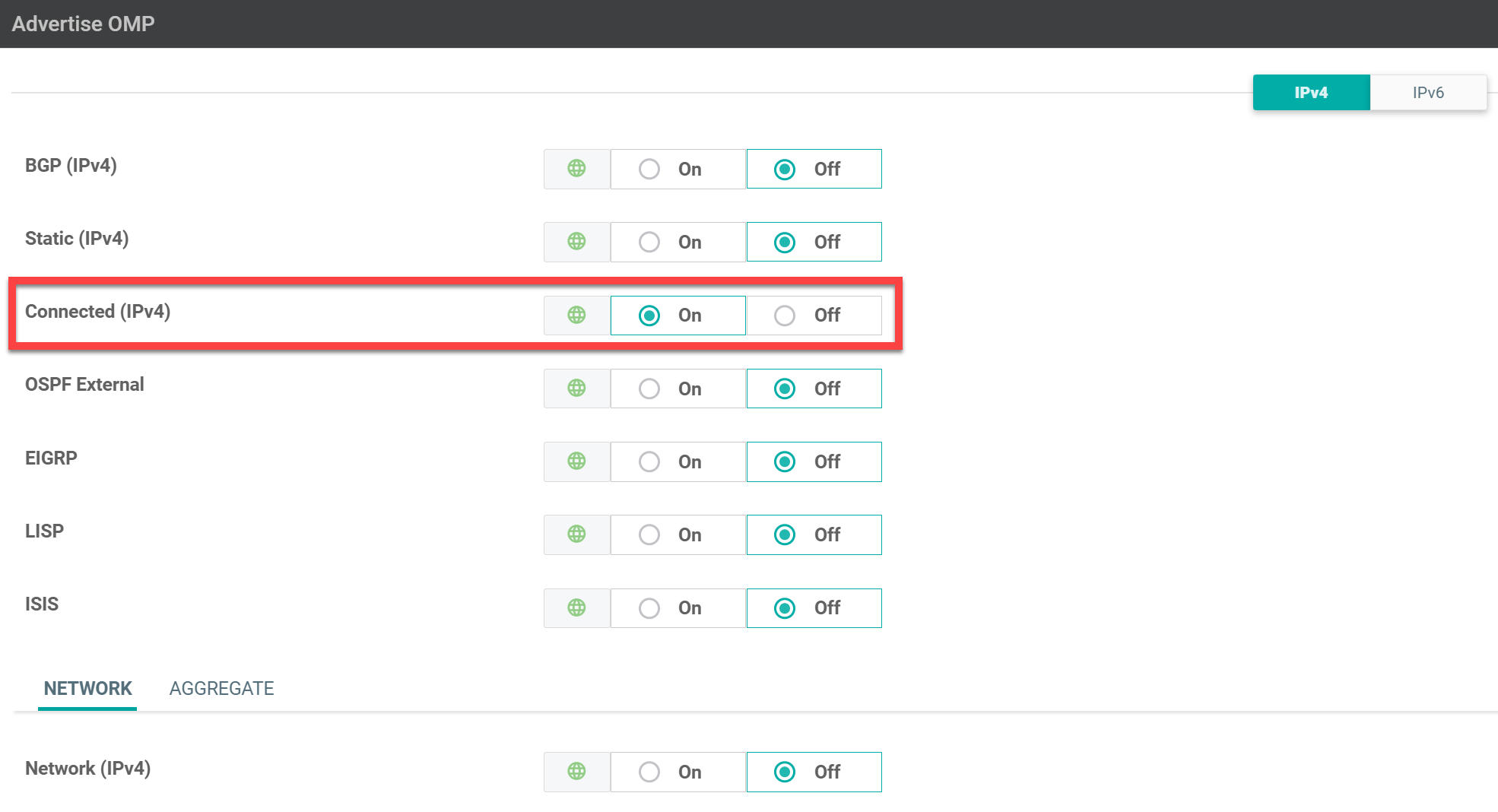
Then, underAdvertise OMP, enable Connected (IPv4):
Click Save to store the template.
Ge0/3 Interface
We need another feature template for the interface that connects to the switch. Click on Add Template and select VPN Interface Ethernet:


Hi @ReneMolenaar and @lagapidis ,
I have tested this with my lab.Service VPN is working fine.But I have some confusion because in my main dashboard it said partial wan connectivity.when I dig deeper I found that BFD sessions between two colors are down.
https://cdn-forum.networklessons.com/uploads/default/original/2X/3/301834d8be0e9ad3fe1419002d5e8097e13a26e4.png
As far as I know WAN edge routers try to form overlay tunnels to every received TLOC from a different site using every available color.So can you please help me to understand this issue.Your help is ... Continue reading in our forum
In vEdge1 why next hop in is towards 10.65.91.100 , why not10.65.92.100…
Hello Himanshu
First of all, in this lab, there is no vEdge1, so I am assuming from the context, that you are referring to the output of vEdge3. Indeed, in the routing table of vEdge3, we see that in order to reach the network of 10.1.0.0/24, it says that the next-hop IP is 10.65.91.100.
Now, this is not necessarily incorrect, since, in the network diagram, you can see that vEdge3 does connect to the biz-internet cloud which is the 10.65.91.0/24 network. And you can see that the exit interface for vEdge3 to reach that network is Ge0/0 which is correctly indic
... Continue reading in our forumHello,
Let’s say I have a router with 3 interfaces: 1 WAN interface and 2 LAN interfaces. The WAN interface is in VPN 0 and other 2 LAN interfaces are in VPN 10 and VPN 20. Are these three interfaces going to be able to talk to each other? If not, why and how can I make them talk to each other? Thanks a lot in advance.
Best Regards,
Azm
Hi @azmuddincisco ,
It is possible to configure route leaking between VPNs yes. It’s called route leaking. Cisco has some examples here:
https://www.cisco.com/c/en/us/td/docs/routers/sdwan/configuration/routing/ios-xe-17/routing-book-xe/m-routing-leaking-for-service-sharing.html
Rene