BGP has a simple loop prevention mechanism for external BGP. When you see your own AS number in the AS path, we do not accept the prefix. This mechanism is fine for Internet routing but there are some other scenarios where this might be an issue. Take a look at the following topology:
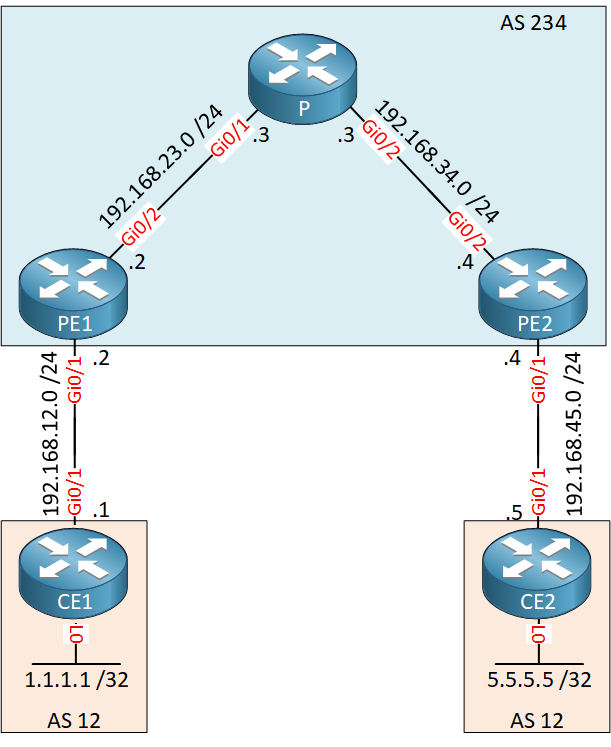
Above we have a small MPLS VPN network with two customer sites. The customer is using the same AS number (12) for both sites. When CE1 or CE2 receive an update from each other they will not accept it since their own AS number will be in the AS path.
Let’s find out if this is true. Here are the configurations of all routers:
Configurations
Here you will find the startup configurations of each device.
CE1
hostname CE1
!
interface Loopback0
ip address 1.1.1.1 255.255.255.255
!
interface GigabitEthernet0/1
ip address 192.168.12.1 255.255.255.0
duplex auto
speed auto
media-type rj45
!
router bgp 12
bgp log-neighbor-changes
network 1.1.1.1 mask 255.255.255.255
neighbor 192.168.12.2 remote-as 234
!
end
PE1
hostname PE1
!
ip vrf CUSTOMER
rd 1:1
route-target export 1:1
route-target import 1:1
!
ip cef
!
interface Loopback0
ip address 2.2.2.2 255.255.255.255
!
interface GigabitEthernet0/1
ip vrf forwarding CUSTOMER
ip address 192.168.12.2 255.255.255.0
duplex auto
speed auto
!
interface GigabitEthernet0/2
ip address 192.168.23.2 255.255.255.0
duplex auto
speed auto
mpls ip
!
router ospf 1
network 2.2.2.2 0.0.0.0 area 0
network 192.168.23.0 0.0.0.255 area 0
!
router bgp 234
bgp log-neighbor-changes
neighbor 4.4.4.4 remote-as 234
neighbor 4.4.4.4 update-source Loopback0
!
address-family ipv4
no neighbor 4.4.4.4 activate
exit-address-family
!
address-family vpnv4
neighbor 4.4.4.4 activate
neighbor 4.4.4.4 send-community extended
exit-address-family
!
address-family ipv4 vrf CUSTOMER
neighbor 192.168.12.1 remote-as 12
neighbor 192.168.12.1 activate
exit-address-family
!
endP
hostname P
!
interface Loopback0
ip address 3.3.3.3 255.255.255.255
!
interface GigabitEthernet0/1
ip address 192.168.23.3 255.255.255.0
duplex auto
speed auto
mpls ip
!
interface GigabitEthernet0/2
ip address 192.168.34.3 255.255.255.0
duplex auto
speed auto
mpls ip
!
router ospf 1
network 3.3.3.3 0.0.0.0 area 0
network 192.168.23.0 0.0.0.255 area 0
network 192.168.34.0 0.0.0.255 area 0
!
endPE2
hostname PE2
!
ip vrf CUSTOMER
rd 1:1
route-target export 1:1
route-target import 1:1
!
ip cef
!
interface Loopback0
ip address 4.4.4.4 255.255.255.255
!
interface GigabitEthernet0/1
ip vrf forwarding CUSTOMER
ip address 192.168.45.4 255.255.255.0
duplex auto
speed auto
!
interface GigabitEthernet0/2
ip address 192.168.34.4 255.255.255.0
duplex auto
speed auto
mpls ip
!
router ospf 1
network 4.4.4.4 0.0.0.0 area 0
network 192.168.34.0 0.0.0.255 area 0
!
router bgp 234
bgp log-neighbor-changes
neighbor 2.2.2.2 remote-as 234
neighbor 2.2.2.2 update-source Loopback0
!
address-family ipv4
no neighbor 2.2.2.2 activate
exit-address-family
!
address-family vpnv4
neighbor 2.2.2.2 activate
neighbor 2.2.2.2 send-community extended
exit-address-family
!
address-family ipv4 vrf CUSTOMER
neighbor 192.168.45.5 remote-as 12
neighbor 192.168.45.5 activate
exit-address-family
!
endCE2
hostname CE2
!
ip cef
!
interface Loopback0
ip address 5.5.5.5 255.255.255.255
!
interface GigabitEthernet0/1
ip address 192.168.45.5 255.255.255.0
duplex auto
speed auto
!
router bgp 12
bgp log-neighbor-changes
network 5.5.5.5 mask 255.255.255.255
neighbor 192.168.45.4 remote-as 234
!
endLet’s find out what is going on. First we’ll check if the PE routers have a VPN route for the prefixes from the CE routers:
PE1#show ip bgp vpnv4 all
Network Next Hop Metric LocPrf Weight Path
Route Distinguisher: 1:1 (default for vrf CUSTOMER)
*> 1.1.1.1/32 192.168.12.1 0 0 12 i
*>i 5.5.5.5/32 4.4.4.4 0 100 0 12 iPE2#show ip bgp vpnv4 all
Network Next Hop Metric LocPrf Weight Path
Route Distinguisher: 1:1 (default for vrf CUSTOMER)
*>i 1.1.1.1/32 2.2.2.2 0 100 0 12 i
*> 5.5.5.5/32 192.168.45.5 0 0 12 iThe PE routers have an entry for the loopback interfaces of the CE routers. Are they advertising these to the CE routers?
PE1#show ip bgp vpnv4 all neighbors 192.168.12.1 advertised-routes
BGP table version is 16, local router ID is 2.2.2.2
Status codes: s suppressed, d damped, h history, * valid, > best, i - internal,
r RIB-failure, S Stale, m multipath, b backup-path, f RT-Filter,
x best-external, a additional-path, c RIB-compressed,
Origin codes: i - IGP, e - EGP, ? - incomplete
RPKI validation codes: V valid, I invalid, N Not found
Network Next Hop Metric LocPrf Weight Path
Route Distinguisher: 1:1 (default for vrf CUSTOMER)
*>i 5.5.5.5/32 4.4.4.4 0 100 0 12 i
Total number of prefixes 1PE2#show ip bgp vpnv4 all neighbors 192.168.45.5 advertised-routes
BGP table version is 18, local router ID is 4.4.4.4
Status codes: s suppressed, d damped, h history, * valid, > best, i - internal,
r RIB-failure, S Stale, m multipath, b backup-path, f RT-Filter,
x best-external, a additional-path, c RIB-compressed,
Origin codes: i - IGP, e - EGP, ? - incomplete
RPKI validation codes: V valid, I invalid, N Not found
Network Next Hop Metric LocPrf Weight Path
Route Distinguisher: 1:1 (default for vrf CUSTOMER)
*>i 1.1.1.1/32 2.2.2.2 0 100 0 12 i
Total number of prefixes 1The PE routers are advertising these to the CE routers. Let’s check the CE routers:
CE1#show ip bgp
Network Next Hop Metric LocPrf Weight Path
*> 1.1.1.1/32 0.0.0.0 0 32768 iCE2#show ip bgp
Network Next Hop Metric LocPrf Weight Path
*> 5.5.5.5/32 0.0.0.0 0 32768 iThere’s nothing there…they only have the prefix on their own loopback interface in the BGP table. Let’s enable a debug on CE1 to figure out why it’s not accepting anything from PE1:
CE1#debug ip bgp all updates
BGP updates debugging is on for all address familiesLet’s reset the neighbor adjacency:
CE1#clear ip bgp *Here’s what you will see:
CE1#
BGP(0): 192.168.12.2 rcv UPDATE about 5.5.5.5/32 -- DENIED due to: AS-PATH contains our own AS;No surprises here…CE1 is denying the update since it sees its own AS number in the AS path. If we want to keep the same AS number on CE1 and CE2 then there are two possible solutions for this issue:
- Allow-AS in: this can be configured on the CE routers which tells them to accept prefixes with their own AS number in the AS path.
- AS override: this can be configured on the PE routers, the AS number will be replaced with the AS number from the service provider.
This lesson is about AS override so that’s what we will do. Let’s configure the PE routers:
PE1(config)#router bgp 234
PE1(config-router)#address-family ipv4 vrf CUSTOMER
PE1(config-router-af)#neighbor 192.168.12.1 as-overridePE2(config)#router bgp 234
PE2(config-router)#address-family ipv4 vrf CUSTOMER
PE2(config-router-af)#neighbor 192.168.45.5 as-overrideTo speed things up, let’s clear the BGP neighbor adjacencies on the PE routers:
PE1 & PE2#clear ip bgp *Let’s take another look at the CE routers:
CE1#show ip bgp 5.5.5.5
BGP routing table entry for 5.5.5.5/32, version 7
Paths: (1 available, best #1, table default)
Not advertised to any peer
Refresh Epoch 1
234 234
192.168.12.2 from 192.168.12.2 (2.2.2.2)
Origin IGP, localpref 100, valid, external, best
rx pathid: 0, tx pathid: 0x0CE2#show ip bgp 1.1.1.1
BGP routing table entry for 1.1.1.1/32, version 7
Paths: (1 available, best #1, table default)
Not advertised to any peer
Refresh Epoch 1
234 234
192.168.45.4 from 192.168.45.4 (4.4.4.4)
Origin IGP, localpref 100, valid, external, best
rx pathid: 0, tx pathid: 0x0The CE routers have now learned each others prefixes. If you take a closer look, you can see that AS number 12 has been replaced with AS number 234.


Hi Rene,
So I’ve learned so far that BGP Allow_AS_IN and BPG Override achieve a similar outcome when confronted with using same ASes for MPLS VPN customer sites that use eBGP for the last mile, but from different end points: CE vs PE. So my question is, is there an advantage/disadvantage using one over another? Or in what context would one method be preferred over another?
Rgds,
Shannon
Shannon,
This is a good question, and there is a lot going on behind the scene to answer it. As you know, AllowAS-In and AS-Override are both essentially tricks that can be used to deal with what would normally be considered a BGP looped route (since the ASN number will appear in the AS Path).
The important consideration is whether the BGP “loop” route will actually be filtered on the PE side or the CE side. AllowAS-In assumes the filtering is being done on the CE side, but in reality, most PEs would have already filtered the route before it got to the CE.
Fo
... Continue reading in our forumHi Andrew,
Awesome response & much appreciated! It’s clear now, thank you.
Rgds,
Shannon
Hi Rene,
Thanks for your nice article !
Is AS Override only support on MPLS environment ??
br//
zaman
Hi Zaman,
It is a BGP feature so it’s not only for MPLS. MPLS VPN however is one of those situations where this can be useful.
Rene