As explained in my first lesson that introduces access-lists, we can use access-lists for filtering (blocking packets) or selecting traffic (for VPNs, NAT, etc).
This also applies to IPv6 access-lists which are very similar to IPv4 access-lists. There are two important differences however:
- IPv4 access-lists can be standard or extended, numbered or named. IPv6 only has named extended access-lists.
- IPv4 access-lists have an invisible implicit deny any at the bottom of every access-list. IPv6 access-lists have three invisible statements at the bottom:
- permit icmp any any nd-na
- permit icmp any any nd-ns
- deny ipv6 any any
The two permit statements are required for neighbor discovery which is an important protocol in IPv6, it’s the replacement for ARP.
Having said that, let’s take a look at the configuration.
Configuration
For this demonstration we only need two routers:
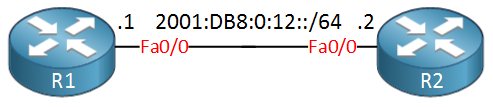
I’ll use subnet 2001:DB8:0:12::/64 in between R1 and R2. To demonstrate the access-list, I’ll create one inbound on R2 and we will try to filter some packets from R1. Let’s take a look at the access-list:
R2(config)#ipv6 access-list ?
WORD User selected string identifying this access list
log-update Control access list log updatesAs you can see above the only option is the named access-list. There’s also no option for standard or extended access-list. Let’s create that access-list:
R2(config)#ipv6 access-list R1_TRAFFICI’ll call it “R1_TRAFFIC”. Here are our options when we create a statement:
R2(config-ipv6-acl)#permit ?
<0-255> An IPv6 protocol number
X:X:X:X::X/<0-128> IPv6 source prefix x:x::y/<z>
ahp Authentication Header Protocol
any Any source prefix
esp Encapsulation Security Payload
host A single source host
icmp Internet Control Message Protocol
ipv6 Any IPv6
pcp Payload Compression Protocol
sctp Streams Control Transmission Protocol
tcp Transmission Control Protocol
udp User Datagram ProtocolThis is similar to IPv4 access-lists. You can pick any protocol you like. Let’s see if we can permit telnet traffic from R1 and deny everything else:


I think you are missing a keyword in this line:
Hi Jeppe,
For sure, not sure what went wrong there. Just fixed it…
Also added my configs at the bottom of the lesson.
Rene
Hi Rene
Will the 3 implicit permit/deny statements won’t show up when we use the show access-list statements?
Thanks
Palani
Palani,
That’s right–the 3 statements will not appear with a show access-list command.
Hi Rene,
I think telnet traffic filter in line vty NOT per interface ? correct me if I wrong.