Lesson Contents
By default the Cisco ASA firewall has a self signed certificate that is regenerated every time you reboot it. This can be an issue when you are using SSL VPN as the web browser of your user will give a warning every time it sees an untrusted certificate. In another lesson where I explained how to configure anyconnect remote access VPN you can see these errors when the remote users connects to the ASA. To fix this problem we have two options:
- Purchase and install an SSL certificate on the ASA from a trusted CA.
- Generate a self signed SSL certificate on the ASA and export it to your user’s computer.
The first option is the best one, you buy an SSL certificate from a provider like Verisign, Entrust, Godaddy, etc. and install it on the ASA. Web browsers have a lot of pre-installed root CA certificates from these providers so when you get a SSL certificate from them, your browser will show them as trusted. This is great because you don’t have to do anything on the user’s computer.
If you don’t want to buy a SSL certificate then we can use the second option. We will generate a SSL certificate on the ASA and self-sign it. This certificate is permanent so it doesn’t dissapear when you reboot the ASA, the problem however is that you have to export and import this certificate on each of your remote users’ computers.
That’s what we will do in this lesson…we will generate the SSL certificate, self-sign it and then export and import it on a remote user’s computer. This is the topology I will use:
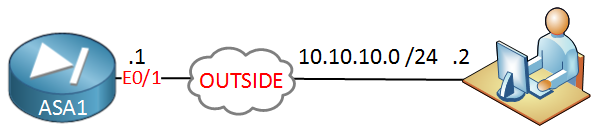
The ASA is connected to a remote user on its outside interface. The user’s computer will run Windows 7. Let’s get started shall we?
ASA Configuration
There are a number of requirements when we work with certificates. First of all we need to configure the correct time, date, assign a hostname and domain name:
ciscoasa(config)# clock set 13:48:00 10 Dec 2014The clock command will work but using NTP to keep your time synchronized would be better. Let’s configure a hostname:
ciscoasa(config)# hostname ASA1
ASA1(config)#I’ll call my device “ASA1”. Now we configure a domain name:
ASA1(config)# domain-name NETWORKLESSONS.LOCALThe domain name will be “NETWORKLESSONS.LOCAL”.
In PKI (Public Key Infrastructure) we need to have keys…a public and private key. When we generate a RSA key it will automatically generate these two keys. The public key can be shared with anyone and is used to encrypt or sign messages. Here’s how to generate the keys:
ASA1(config)# crypto key generate rsa label MY_RSA_KEY modulus 1024
INFO: The name for the keys will be: MY_RSA_KEY
Keypair generation process begin. Please wait...The key pair is called “MY_RSA_KEY”. You can see them here:
ASA1(config)# show crypto key mypubkey rsa | begin MY_RSA_KEY
Key name: MY_RSA_KEY
Usage: General Purpose Key
Modulus Size (bits): 1024
Key Data:
30819f30 0d06092a 864886f7 0d010101 05000381 8d003081 89028181 00ac99a2
2fc2907a 1e86ddf4 503dc102 72611d80 77ed5762 a857b297 ee609520 469c2dbe
f50c5ce1 ac39cba1 998f9504 93f8bfbd ddfaadf7 0cc1f322 f20a24b0 db7fd9e5
61a024d1 9f6f5380 562e7848 017e0f88 167732c5 aef50f80 e6431420 0745b9f4
9217f9df 31ca5a2f 05fe6af6 efb388d4 24a22355 7112458f c20f022f 7f020301
0001We now have to create a “trustpoint”. The trustpoint is a container where certificates are stored. This is where we configure parameters like the FQDN, subject name, keypair, etc:
ASA1(config)# crypto ca trustpoint SELF_TRUSTPOINT
ASA1(config-ca-trustpoint)# enrollment self
ASA1(config-ca-trustpoint)# fqdn ASA1.NETWORKLESSONS.LOCAL
ASA1(config-ca-trustpoint)# subject-name CN=ASA1.NETWORKLESSONS.LOCAL
ASA1(config-ca-trustpoint)# keypair MY_RSA_KEYThe trustpoint is called “SELF_TRUSTPOINT” and the enrollment self command means that the ASA will sign its own certificates. The certificate will be assigned to ASA1.NETWORKLESSONS.LOCAL. We will use the RSA keypair that we just generated. We can now enroll the actual certificate:
ASA1(config)# crypto ca enroll SELF_TRUSTPOINT
% The fully-qualified domain name in the certificate will be: ASA1.NETWORKLESSONS.LOCAL
% Include the device serial number in the subject name? [yes/no]: no
Generate Self-Signed Certificate? [yes/no]: yesThe certificate is now enrolled. We can see it here:


Hello Chris
That sounds like a great idea. I suggest you go to the Member Ideas section of the site and post a suggestion to have the topic added.
https://networklessons.com/member-ideas
I hope this has been helpful!
Laz
I already try the configuration on the Anyconnect self-signed certificate , but I already get
no valid certificate available for authentication. When I write the commandsh crypto sslthe result is :does this error has to do with
Certificate authentication is not enablemessage?Hello Alvaro
The “no valid certificate available for authentication” error message usually indicates that the client does not have a valid certificate that can be used for authentication. To resolve this issue, you will need to ensure that the client has a valid certificate that meets the requirements of the server. Some things you can check include the following:
- Have you imported the certificate to the user’s computer successfully?
- What kind of error message do you receive on the client’s screen?
- Are there any other indications on the ASA of the attempted
... Continue reading in our forum