Lesson Contents
Cisco Catalyst Switches have a feature called SPAN (Switch Port Analyzer) that lets you copy all traffic from a source port or VLAN to a destination interface. This is very useful for several reasons:
- If you want to use wireshark to capture traffic from an interface that is connected to a workstation, server, phone, or anything else you want to sniff.
- Redirect all traffic from a VLAN to an IDS / IPS.
- Redirect all VoIP calls from a VLAN so you can record the calls.
The source can be an interface or a VLAN. The destination is an interface. You can choose to forward transmitted, received, or both directions to the destination interface.
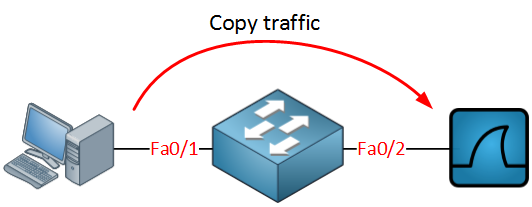
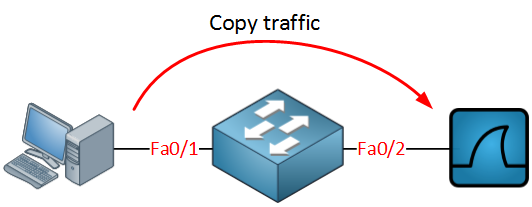
When you use a destination interface on the same switch as your switch we call it SPAN, when the destination is a remote interface on another switch we call it RSPAN (Remote SPAN). When using RSPAN, you need to use a VLAN for your RSPAN traffic so that traffic can travel from the source switch to the destination switch.
When you use RSPAN, you need to use a VLAN that carries the traffic that you are copying. In the picture above, you see SW1, which will copy the traffic from the computer onto a “RSPAN VLAN”. SW2 doesn’t do anything with it while SW3 receives the traffic and forwards it to a computer that has wireshark running. Make sure the trunks between the switches allow the RSPAN VLAN.
SPAN and RSPAN are great, but there are a couple of things you need to keep in mind…
Restrictions
Both SPAN and RSPAN have some restrictions. I’ll give you an overview of the most important ones:
- The source interface can be anything…switchport, routed port, access port, trunk port, etherchannel, etc.
- When you configure a trunk as the source interface, it will copy traffic from all VLANs; however, there is an option to filter this.
- You can use multiple source interfaces or multiple VLANs, but you can’t mix interfaces and VLANs.
- It’s very simple to overload an interface. When you select an entire VLAN as the source and use a 100Mbit destination interface…it might be too much.
- When you configure a destination port, you will “lose” its configuration. By default, the destination interface will only be used to forward SPAN traffic to. However, it can be configured to permit incoming traffic from a device that is connected to the destination interface.
- Layer 2 frames like CDP, VTP, DTP, and spanning tree BPDUs are not copied by default, but you can tell SPAN/RSPAN to copy them anyway.
This should give you an idea of what SPAN / RSPAN is capable of. The configuration is pretty straightforward so let me give you some examples…
SPAN Configuration
Let’s start with a simple configuration. I will use the example I showed you earlier:
Switch(config)#monitor session 1 source interface fa0/1
Switch(config)#monitor session 1 destination interface fa0/2You can verify the configuration like this:
Switch#show monitor session 1
Session 1
---------
Type : Local Session
Source Ports :
Both : Fa0/1
Destination Ports : Fa0/2
Encapsulation : Native
Ingress : DisabledAs you can see, by default, it will copy traffic that is transmitted and received (both) to the destination port. If you only want the capture the traffic going in one direction, you have to specify it like this:
Switch(config)#monitor session 1 source interface fa0/1 ?
, Specify another range of interfaces
- Specify a range of interfaces
both Monitor received and transmitted traffic
rx Monitor received traffic only
tx Monitor transmitted traffic onlyJust add rx or tx, and you are ready to go. If interface FastEthernet 0/1 were a trunk, you could add a filter to select the VLANs you want to forward:
Switch(config)#monitor session 1 filter vlan 1 - 100This filter above will only forward VLAN 1 – 100 to the destination. If you don’t want to use an interface as the source but a VLAN, you can do it like this:
Switch(config)#monitor session 2 source vlan 1
Switch(config)#monitor session 2 destination interface fa0/3I cannot use session 1 for this because I am already using source interfaces for that session. It’s also impossible to use the same destination interface for another session. I created another session number and picked FastEthernet 0/3 as a destination.
Configurations
Want to take a look for yourself? Here you will find the final configuration of each device.
Switch
hostname Switch
!
monitor session 1 source interface Fa0/1
monitor session 1 destination interface Fa0/2
monitor session 2 source vlan 1
monitor session 2 destination interface Fa0/3
endSo far so good? Let’s look at RSPAN!
RSPAN Configuration
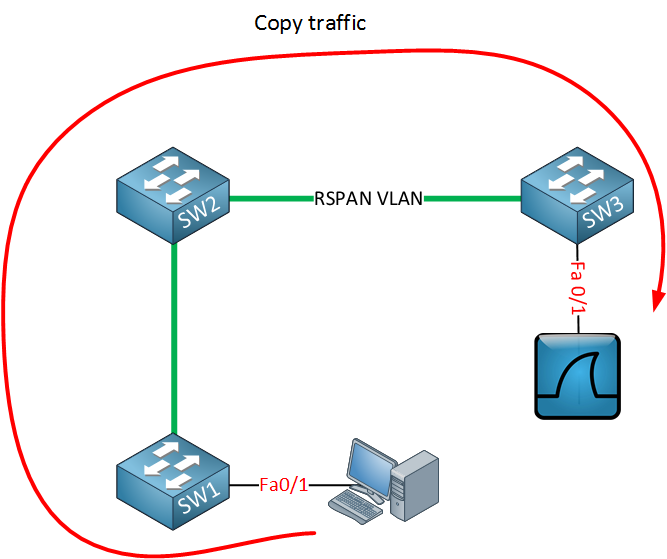
To demonstrate RSPAN, I will use a topology with two switches:
The idea is to forward traffic from FastEthernet 0/1 on SW1 to FastEthernet 0/1 on SW2. There are a couple of things we have to configure here:
SW1(config)#vlan 100
SW1(config-vlan)#remote-spanSW2(config)#vlan 100
SW2(config-vlan)#remote-spanFirst, we need to create the VLAN and tell the switches that it’s an RSPAN vlan. This is something that is easily forgotten. Secondly, we will configure the link between the two switches as a trunk:


Thanks, Rene. Do you think its worth to taught us about ERSPAN?
Hi Rene,
I am unable to understand what is the maximum SPAN session limit ?
a) how many src / dst ports can be included in a SPAN session
b) if we specify session 1 for both src and destination, does that means that only 1 session is used up ? or src = 1 session, dst = 1 session total = 2 session
c) what is the maximum limit of SPAN session that can be created ? (is it base on src, destination combi or ?)
You can take 2960x as a reference. Try reading the manual but can’t figure the exact meaning out
Regards,
Alan
Hi Alan,
Good question…only thing I could find is this document:
https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst2960x/software/15-0_2_EX/network_management/configuration_guide/b_nm_15ex_2960-x_cg/b_nm_15ex_2960-x_cg_chapter_0111.html#concept_A4AB227AC35840A1ACE51453EDBACD3E
a) It doesn’t specify anything about the number of interfaces, only the number of sessions.
b) For a single session, you specify a source + destination so that’s one session.
c) maximum of 4 (2 if switch is stacked with Catalyst 2960-S switches) source sessions and 64 RSPAN dest
... Continue reading in our forumHello Rene,
As a CCIE course for SPAN & RSPAN , i think you need to add ERSPAN also to the CCIE course on SPAN &RSPAN , because this course is the same as in the Switching CCNP. Please clarified about that.
Hi Sinan,
I agree, it’s on the list. It seems ERSPAN can be configured on the CSR1000V routers.
Rene