Lesson Contents
OSPF packets are unauthenticated by default, which is a security risk. If you receive OSPF hello packets on an interface, you can send hello packets on your own and establish a neighbor adjacency. This way, an attacker could inject malicious routes. With MD5 authentication, you can authenticate OSPF packets. Instead of sending a password in plain text, we use MD5 cryptographic hashing. MD5 is no longer considered secure however which is why OSPF also supports HMAC-SHA authentication nowadays.
Key Takeaways
- MD5 authentication uses cryptographic hashing to secure OSPF routing updates
- Enable this with two interface commands:
ip ospf message-digest-key X md5 PASSWORDip ospf authentication message-digest
- Key IDs must match on both routers, but the number itself can be any value
- Can be enabled per-interface or for an entire OSPF area with the
area 0 authentication message-digestcommand underrouter ospf - Use
show ip ospf interfaceanddebug ip ospfcommands to verify and troubleshoot - No longer considered secure because MD5 is a weak hashing algorithm.
Prerequisites
To follow this lesson, you should have basic understanding of OSPF and plain text OSPF authentication.
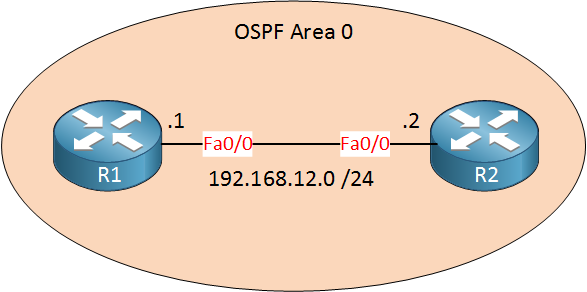
In a previous lesson, I demonstrated how to configure plain text authentication for OSPF. This time we’ll look at MD5 authentication. The idea is the same, but some of the commands are different. Anyway, here is the topology that we will use:
Just two routers in the same area, nothing special. Here is the configuration to enable MD5 authentication:
R1(config)#interface fastEthernet 0/0
R1(config-if)#ip ospf message-digest-key 1 md5 MYPASS
R1(config-if)#ip ospf authentication message-digestR2(config)#interface fastEthernet 0/0
R2(config-if)#ip ospf message-digest-key 1 md5 MYPASS
R2(config-if)#ip ospf authentication message-digestFor MD5 authentication, you need different commands. First, use ip ospf message-digest-key X md5 to specify the key number and password. It doesn’t matter which key number you choose, but it has to be the same on both ends. To enable OSPF authentication, you need to type in ip ospf authentication message-digest.
It is also possible to enable authentication for the entire area. This way, you don’t have to use the ip ospf authentication message-digest command on all of your interfaces to activate it. Here’s the command to enable MD5 authentication for the entire area:
R1(config)#router ospf 1
R1(config-router)#area 0 authentication message-digestThat’s all we have to do. Let’s verify our work…
Verification
R1#show ip ospf interface fastEthernet 0/0
FastEthernet0/0 is up, line protocol is up
Internet Address 192.168.12.1/24, Area 0
Process ID 1, Router ID 192.168.12.1, Network Type BROADCAST, Cost: 1
Transmit Delay is 1 sec, State BDR, Priority 1
Designated Router (ID) 192.168.12.2, Interface address 192.168.12.2
Backup Designated router (ID) 192.168.12.1, Interface address 192.168.12.1
Flush timer for old DR LSA due in 00:01:53
Timer intervals configured, Hello 10, Dead 40, Wait 40, Retransmit 5
oob-resync timeout 40
Hello due in 00:00:05
Supports Link-local Signaling (LLS)
Index 1/1, flood queue length 0
Next 0x0(0)/0x0(0)
Last flood scan length is 1, maximum is 1
Last flood scan time is 0 msec, maximum is 0 msec
Neighbor Count is 1, Adjacent neighbor count is 1
Adjacent with neighbor 192.168.12.2 (Designated Router)
Suppress hello for 0 neighbor(s)
Message digest authentication enabled
Youngest key id is 1Using show ip ospf interface we see MD5 authentication is enabled, and we are using key ID 1. We have a neighbor, so it seems to be working. Let’s try a debug:
R1#debug ip ospf packet
OSPF packet debugging is on
OSPF: rcv. v:2 t:1 l:48 rid:192.168.12.2
aid:0.0.0.0 chk:0 aut:2 keyid:1 seq:0x3C7EC653 from FastEthernet0/0Debug shows us that MD5 authentication is enabled (aut:2), and we use key ID 1. Debug is also great for fixing authentication errors. Here’s why:
R1(config)#interface fastEthernet 0/0
R1(config-if)#no ip ospf message-digest-key 1 md5 MYPASS
R1(config-if)#ip ospf message-digest-key 1 md5 MYWRONGPASSFirst, we’ll enter the wrong password. Now I’ll enable a debug and reset the OSPF process:
R1#debug ip ospf adj
OSPF adjacency events debugging is onR1#clear ip ospf process
Reset ALL OSPF processes? [no]: yesHere’s what you will see:
R1#
OSPF: Rcv pkt from 192.168.12.2, FastEthernet0/0 : Mismatch Authentication Key - Message Digest Key 1Somewhere in the debug, you’ll see the message above. This means that we are using MD5 key ID 1 on both sides, but the password is incorrect.


thank you so much.. this helped me
Rene… in order to configure MD5 for an entire area… do we have to (at a minimum) configure a single subnet first - interface on Router A and connecting interface on Router B – using the
Does that have to be done first? If yes – then the - Area 1 authentication message digest – command applies authentication to every other router and its interface in the entire area? … with the same key and password?
Hi Jason,
If you enable those two commands on the interface then MD5 authentication will be used, but only if the interface is running OSPF. You need to make sure you have a network command that covers the subnet of the interface. Otherwise…the interface won’t run OSPF so we also won’t have any authentication
Rene
Easy to understand, Thanks.
what if i have instances of different OSPF area, and I want the different areas to communicate. is it still the exact same or I need to have a different key number and the same password.