Lesson Contents
Locally configured usernames and passwords can become an administrative nightmare if you have a network with many network devices. Each time you want to add a username or change a password, you have to log in each device one-by-one to add or change something. It’s a better idea to work with a central AAA server for authentication. On this server, you add all your usernames and passwords. You configure your routers and switches to use this AAA server for authentication.
On Cisco IOS, you can configure precisely how you want to use the AAA server for authentication. You can use it for console or VTY access but also for enable (privileged) mode and some other options like PPP authentication.
In this lesson, I will show you how to configure AAA authentication on a Cisco IOS router. We will use a RADIUS server with the FreeRADIUS software. FreeRADIUS is (as the name implies) free and easy to configure. Once everything is configured, a user that wants to access the console and use privileged mode will be authenticated by the RADIUS server.
Configuration
Here is the topology that I will use:
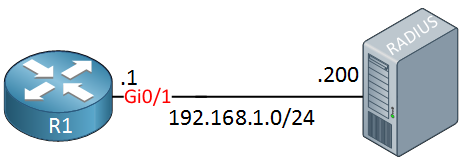
We have a router and the RADIUS server. Let’s start with the configuration of FreeRADIUS .
FreeRADIUS
FreeRADIUS runs on Linux and most Linux distributions have it in their repositories. I’m using a Ubuntu server and you can use apt-get to install it:
# apt-get install freeradius freeradius-utilsOnce installed, we have to make some changes to the default configuration files. The first thing to do, is add a new client (our router). Edit the clients.conf file with your favorite text editor:
# vim /etc/freeradius/clients.confAnd add an entry at the bottom that looks like this:
client 192.168.1.1 {
secret = MY_KEY
nastype = cisco
shortname = router
}My client has an IP address of 192.168.1.1 (the router) and the secret is “MY_KEY”. We will later configure this on the router.
Let’s add a user account, this will be used by the admin that wants access to the router. Open the users file:
# vim /etc/freeradius/usersAnd at the end of this file, create an entry that looks like this:
REMOTE_ADMIN Cleartext-Password := "MY_PASSWORD"
Service-Type = NAS-Prompt-UserThis allows user account “REMOTE_ADMIN” to log in with password “MY_PASSWORD”. We will also add an entry for enable (privileged) mode:
$enab15$ Cleartext-Password := "REMOTE_ENABLE"
Service-Type = NAS-Prompt-UserThe password to access enable mode will be “REMOTE_ENABLE”. Save the users file and exit.
Now we have to (re)start FreeRADIUS to apply these changes:
# /etc/init.d/freeradius restart
freeradius stop/waiting
freeradius start/running, process 18145FreeRADIUS runs as a service but when you are testing things in a lab, it’s easier to run it in debug mode. This allows you to see incoming authentication requests and debug when things go wrong. If you want to do this, you first have to stop the service:
# /etc/init.d/freeradius stop
freeradius stop/waitingAnd now you can start it in debug mode:
# freeradius -XIt will produce some messages and then shows you that it’s ready to process requests:
Listening on authentication address * port 1812
Listening on accounting address * port 1813
Listening on authentication address 127.0.0.1 port 18120 as server inner-tunnel
Listening on proxy address * port 1814
Ready to process requests.Whenever a client asks FreeRADIUS for authentication, it will now show up on the console.
Cisco IOS
Our router is configured by default to use no or local authentication. That’s something we have to change. First you need to enable the AAA commands:
R1(config)#aaa new-modelThis gives us access to some AAA commands. Let’s configure the RADIUS server that you want to use:
R1(config)#radius server MY_RADIUS
R1(config-radius-server)#address ipv4 192.168.1.200 auth-port 1812 acct-port 1813
R1(config-radius-server)#key MY_KEYYou can pick whatever name you want for the RADIUS server, I’ll call mine “MY_RADIUS”. We do have to configure its IP address and it’s a good idea to specify the authentication (and accounting) port(s). The official ports for RADIUS authentication and accounting are 1812 and 1813. Before IANA allocated these ports, port number 1645 and 1646 were used unofficially, many RADIUS servers/clients still use these ports.
Now we can configure the router to use our RADIUS server for authentication. Let’s check the aaa authentication command:
R1(config)#aaa authentication ?
arap Set authentication lists for arap.
attempts Set the maximum number of authentication attempts
banner Message to use when starting login/authentication.
dot1x Set authentication lists for IEEE 802.1x.
enable Set authentication list for enable.
eou Set authentication lists for EAPoUDP
fail-message Message to use for failed login/authentication.
login Set authentication lists for logins.
password-prompt Text to use when prompting for a password
ppp Set authentication lists for ppp.
sgbp Set authentication lists for sgbp.
suppress Do not send access request for a specific type of user.
username-prompt Text to use when prompting for a usernameThere is quite some stuff that we can use the RADIUS server for. Login and enable is what we are going to. Dot1x is another popular choice on switches for per-port authentication. That’s something I covered in another lesson.
Let’s look at the login options:
R1(config)#aaa authentication login ?
WORD Named authentication list (max 31 characters, longer will be
rejected).
default The default authentication list.Here we have to choose an authentication list. Cisco IOS uses the default list for the console, VTY lines (telnet or SSH) and the AUX port. If you want to use AAA authentication for all these methods then you can use the default list. If you only want to use AAA authentication for the console and not for the VTY and AUX port then it might be better to use a new authentication list.
I will use the default authentication list so that AAA authentication is used for the console and AUX port. I’ll show you how I can exclude the VTY lines.
Let’s look at the options of the default list:
R1(config)#aaa authentication login default ?
cache Use Cached-group
enable Use enable password for authentication.
group Use Server-group
krb5 Use Kerberos 5 authentication.
krb5-telnet Allow logins only if already authenticated via Kerberos V
Telnet.
line Use line password for authentication.
local Use local username authentication.
local-case Use case-sensitive local username authentication.
none NO authentication.
passwd-expiry enable the login list to provide password aging supportFirst, we will configure the servers that we want to use:
R1(config)#aaa authentication login default group ?
WORD Server-group name
ldap Use list of all LDAP hosts.
radius Use list of all Radius hosts.
tacacs+ Use list of all Tacacs+ hosts.We only have one RADIUS server configured so let’s go for all RADIUS hosts. If you have a lot of RADIUS servers then it’s also possible to create a server group that contains the RADIUS servers you want to use. Let’s continue:
R1(config)#aaa authentication login default group radius ?
cache Use Cached-group
enable Use enable password for authentication.
group Use Server-group
krb5 Use Kerberos 5 authentication.
line Use line password for authentication.
local Use local username authentication.
local-case Use case-sensitive local username authentication.
none NO authentication.
<cr>Besides the RADIUS server, we can choose a fallback option. If our RADIUS server is unreachable, do you want all authentication to fail or perhaps fall back to some local usernames and passwords of the router? Let’s add local fall back authentication:


Hello Laz,
Would you please explain the functionalities of the below commands at your convenient time? Thank you so much in advance.
Best Regards,
Az
Hello Azm!
All of these commands involve the accounting of users connecting to the device as well as of events that occur on the device. Specifically, accounting management in this context is a mechanism that allows you to track individual and group usage of network resources. The different commands above configure what, how and when this information is recorded. Accounting information can be stored locally on the device, but more commonly is sent to an AAA (Authentication, Authorization and Accounting) server.
You can find detailed information about the
... Continue reading in our forumaaaHello Laz,
Thank you for your reply. However, still it’s little bit fuzzy to me. Would you please break it down once again with a real life example? Thank you again.
Best Regards,
Azm Uddin
Hello Azm
Let’s say I have a router on site and I want to keep track of all of the command line activity. Specifically, I want to monitor all of the commands that are entered in the executive mode command line and the processes they invoke. Since I have a TACACS+ server on site, I decide to use that as my accounting server. (I can use RADIUS as well). Lets say I have two TACACS+ servers at 10.10.10.31 and 10.10.10.32.
The first thing I would do is create an AAA group called my_server_group using the following commands:
... Continue reading in our forumHello Laz,
great explanation as usual. A few questions. If I use
**aaa accounting exec default start-stop**command,**aaa accounting commands 1 default stop-only**and**aaa accounting commands 15 default stop-only**do not need to be used because the first one will cover everything. Correct? Would you also please explain the below commands:Thank you so much.
Best regards,
Azm Uddin