Lesson Contents
On most networks, you will see a wide range of applications. Each application is unique and has its requirements when it comes to bandwidth, delay, jitter, etc. For example, an FTP application used for backups of large files might require a lot of bandwidth but delay and jitter won’t matter since it’s not an interactive application.
Voice over IP, on the other hand, doesn’t require much bandwidth but delay and jitter are very important. When your delay is too high, your calls will become walkie-talkie conversations, and jitter screws up the sound quality.
To make sure each application gets the treatment that it requires, we have to implement QoS (Quality of Service).
The first step when implementing QoS is classification. That’s what this lesson is all about.
By default, your router doesn’t care what kind of IP packets it is forwarding…the only important thing is looking at the destination IP address, doing a routing table lookup, and whoosh…the IP packet has been forwarded.
Before we can configure any QoS methods like queuing, policing, or shaping, we have to look at the traffic that is running through our router and identify (classify) it so we know to which application it belongs. That’s what classification is about.
Once the traffic has been classified, we will mark it and apply a QoS policy to it. Marking and configuring QoS policies are a whole different story so in this lesson, we’ll just stick to classification.
On IOS routers, there are a couple of methods we can use for classification:
- Header inspection
- Payload inspection
There are quite some fields in our headers that we can use to classify applications. For example, telnet uses TCP port 23 and HTTP uses TCP port 80. Using header inspection, you can look for the following:
- Layer 2: MAC addresses
- Layer 3: source and destination IP addresses
- Layer 4: source and destination port numbers and protocol
This is a straightforward method of classification that works well but has some downsides. For example, you can configure your router so that everything that uses TCP and destination port number 80 is “HTTP”, but it’s possible that some other applications (instant messaging, for example) are also using TCP port 80. Your router will perform the same action for IM and HTTP traffic.
Payload inspection is more reliable as it will do deep packet inspection. Instead of just looking at layer 2/3/4 information, the router will look at the contents of the payload and will recognize the application. On Cisco IOS routers this is done with NBAR (Network-Based Application Recognition).
When you enable NBAR on an interface, the router will inspect all incoming IP packets and try to match them with signatures and attributes in the PDLM (Packet Description Language Module). For example, NBAR can detect HTTP traffic no matter what ports you are using, and it can also match things like:
- URL
- MIME-type (zip file, image, etc.)
- User-agent (Mozilla, Opera, etc.)
Since NBAR can see the URL, it is also commonly used to block websites and is a popular choice for classification.
You should now have an idea of what classification is about, let’s look at some routers and configure classification.
Configuration
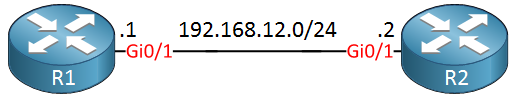
We’ll start with a simple example where I use an access-list to classify some telnet traffic. Here’s the topology that I will use:
R1 will be our telnet client and R2 the telnet server. We will classify the packets when they arrive at R2. Let’s look at the configuration!
Classification with access-list
First, I have to create an access-list that matches telnet traffic:
R2(config)#ip access-list extended TCP_PORT_23
R2(config-ext-nacl)#permit tcp any any eq 23This will match all IP packets that use TCP as the transport protocol and destination port 23. Normally when you configure an access-list for filtering, we apply it to the interface. When configuring QoS, we have to use the MQC (Modular Quality of Service Command-Line Interface). The name is pretty spectacular but it’s a really simple method to configure QoS.
We use something called a policy-map where we configure the QoS actions we want to perform…marking, queueing, policing, shaping, etc. These actions are performed on a class-map, and that’s where we specify the traffic. Let me show you how this is done:
R2(config)class-map TELNET
R2(config-cmap)#match ?
access-group Access group
any Any packets
class-map Class map
cos IEEE 802.1Q/ISL class of service/user priority values
destination-address Destination address
discard-class Discard behavior identifier
dscp Match DSCP in IP(v4) and IPv6 packets
flow Flow based QoS parameters
fr-de Match on Frame-relay DE bit
fr-dlci Match on fr-dlci
input-interface Select an input interface to match
ip IP specific values
mpls Multi Protocol Label Switching specific values
not Negate this match result
packet Layer 3 Packet length
precedence Match Precedence in IP(v4) and IPv6 packets
protocol Protocol
qos-group Qos-group
source-address Source address
vlan VLANs to matchI created a class-map called “TELNET”, and when you create a class-map, you have a lot of options. On top, you see access-group which uses an access-list to classify the traffic, that’s what I will use. Some other nice methods are the input interface, frame-relay DLCI values, packet length, etc. The most simple option is probably the access-list:
R2(config-cmap)#match access-group name TCP_PORT_23My class-map called “TELNET” now matches traffic that is specified in the access-list called “TCP_PORT_23”.
Now, we can create a policy-map and refer to our class-map:
R2(config)#policy-map CLASSIFY
R2(config-pmap)#class TELNETThe policy-map is called “CLASSIFY” and the class-map called “TELNET” belongs to it. Normally this is where I also specify the QoS action like marking, queueing, etc. I’m not configuring any action right since this lesson is only about classification.
Before the policy-map does anything, we have to attach it to an interface:
R2(config)#interface GigabitEthernet 0/1
R2(config-if)#service-policy input CLASSIFYThat’s it. Our router can now classify telnet traffic. Let’s try it by telnetting from R1 to R2:
R1#telnet 192.168.12.2
Trying 192.168.12.2 ... OpenLet’s see what R2 thinks of this:
R2#show policy-map interface GigabitEthernet 0/1
GigabitEthernet0/1
Service-policy input: CLASSIFY
Class-map: TELNET (match-all)
11 packets, 669 bytes
5 minute offered rate 0 bps
Match: access-group name TCP_PORT_23
Class-map: class-default (match-any)
3 packets, 206 bytes
5 minute offered rate 0 bps, drop rate 0 bps
Match: anyGreat! Our router sees the telnet traffic that arrives on the GigabitEthernet 0/1 interface. You can see the name of the policy-map, the class-map, and the access-list that we used. Something that you should remember is that all traffic that is not specified in a class-map will hit the class-default class-map. Not too bad, right? Let’s see if we can also make this work with NBAR…
Classification with NBAR
The configuration of NBAR is quite easy. First, let me show you a simple example of NBAR where it shows us all traffic that is flowing through an interface:
R2(config)#interface GigabitEthernet 0/1
R2(config-if)#ip nbar protocol-discoveryNow you can view all traffic that is flowing through the interface:
R2#show ip nbar protocol-discovery
GigabitEthernet0/1
Last clearing of "show ip nbar protocol-discovery" counters 00:00:20
Input Output
----- ------
Protocol Packet Count Packet Count
Byte Count Byte Count
5min Bit Rate (bps) 5min Bit Rate (bps)
5min Max Bit Rate (bps) 5min Max Bit Rate (bps)
------------------------ ------------------------ ------------------------
telnet 8 7
489 457
0 0
0 0
unknown 3 2
180 120
0 0
0 0
Total 11 9
669 577
0 0
0 0I don’t have a lot going on on this router, but telnet is there. This is a nice way to see the different traffic types on your interface, but if we want to use this information for QoS, we have to put NBAR in a class-map. Here’s how:
R2(config)#class-map NBAR-TELNET
R2(config-cmap)#match protocol ?
3com-amp3 3Com AMP3
3com-tsmux 3Com TSMUX
3pc Third Party Connect Protocol
914c/g Texas Instruments 914 Terminal
9pfs Plan 9 file service
CAIlic Computer Associates Intl License Server
Konspire2b konspire2b p2p network
acap ACAP
acas ACA Services
accessbuilder Access Builder
accessnetwork Access Network
acp Aeolon Core Protocol
acr-nema ACR-NEMA Digital Img
aed-512 AED 512 Emulation service
agentx AgentX
alpes Alpes
aminet AMInet
an Active Networks
anet ATEXSSTR
ansanotify ANSA REX Notify
ansatrader ansatrader
aodv AODV
[output omitted]I created a class-map called “NBAR-TELNET”, and when I use match protocol you can see there’s a long list of supported applications. I’m not going to show all of it, but telnet is in there somewhere:
R2(config-cmap)#match protocol telnetThat’s how we use NBAR in a class-map. Now, we need to add this class-map to the policy-map:
R2(config)#policy-map CLASSIFY
R2(config-pmap)#no class TELNET
R2(config-pmap)#class NBAR-TELNETI’ll remove the old class-map with the access-list and add the new class-map to our policy-map.


Thank you very much. This is really very good topic and it is very clear to me.
Thanks Renee! I’m gaining some traction on QOS
Hello Renee
Thanks for your excellent introduction!
Here I have one concern, which “Tool” is better to identify the specific traffic? For example, If want to perform QoS for one of applications named ABC, how does router know which traffic is for Application - ABC?
Thanks
Dong
Hi Dong,
If it’s a well known application like HTTP, HTTPS, SMTP, POP3, IMAP, SQL, etc. then NBAR can recognize them. Otherwise, it’s best to use an access-list to match the port numbers of your application.
Rene
Hello Rene
Thanks for your feedback, and then, what’s the best way to get the port numbers of some particular applications?
Thanks
Dong