Trunks are required to carry VLAN traffic from one switch to another. This lesson will demonstrate how to configure a trunk between Cisco Catalyst switches. Let me show you the topology that we’ll use:
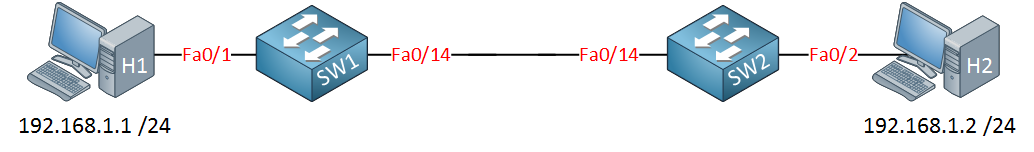
Above, you see a topology with a computer connected to each switch. We’ll put the computers in the same VLAN and create a trunk between the two switches.
Let’s start by creating a VLAN:
SW1(config)#vlan 50 SW1(config-vlan)#name Computers SW1(config-vlan)#exit
SW2(config)#vlan 50 SW2(config-vlan)#name Computers SW2(config-vlan)#exit
And let’s put the interfaces connected to the computers in the correct VLAN:
SW1(config)#interface fa0/1 SW1(config-if)#switchport access vlan 50
SW2(config)#interface fa0/2 SW2(config-if)#switchport access vlan 50
The next step is to create a trunk between the two switches. Technically the interfaces between the two switches can also be in access mode right now because I only have a single VLAN.
SW1(config)#interface fa0/14 SW1(config-if)#switchport mode trunk Command rejected: An interface whose trunk encapsulation is "Auto" can not be configured to "trunk" mode.
SW2(config)#interface fa0/14 SW2(config-if)#switchport mode trunk Command rejected: An interface whose trunk encapsulation is "Auto" can not be configured to "trunk" mode.
I try to change the interface to trunk mode with the switchport mode trunk command. Depending on the switch model, you might see the same error as me. If we want to change the interface to trunk mode, we need to change the trunk encapsulation type. Let’s see what options we have:
SW1(config-if)#switchport trunk encapsulation ? dot1q Interface uses only 802.1q trunking encapsulation when trunking isl Interface uses only ISL trunking encapsulation when trunking negotiate Device will negotiate trunking encapsulation with peer on interface
This is where you can choose between 802.1Q or ISL encapsulation. By default, our switch will negotiate about the trunk encapsulation type.
SW1(config-if)#switchport trunk encapsulation dot1q
SW2(config-if)#switchport trunk encapsulation dot1q
Let‟s change it to 802.1Q by using the switchport trunk encapsulation command.
SW1#show interfaces fa0/14 switchport
Name: Fa0/14
Switchport: Enabled
Administrative Mode: dynamic auto
Operational Mode: static access
Administrative Trunking Encapsulation: dot1q
SW2#show interfaces fa0/14 switchport
Name: Fa0/14
Switchport: Enabled
Administrative Mode: dynamic auto
Operational Mode: static access
Administrative Trunking Encapsulation: dot1q
As you can see the trunk encapsulation is now 802.1Q.
SW1(config)#interface fa0/14 SW1(config-if)#switchport mode trunk
SW2(config)#interface fa0/14 SW2(config-if)#switchport mode trunk
Now I can successfully change the switchport mode to trunk.
SW1#show interfaces fa0/14 switchport
Name: Fa0/14
Switchport: Enabled Administrative Mode: trunk Operational Mode: trunk
Administrative Trunking Encapsulation: dot1q
Operational Trunking Encapsulation: dot1q
SW2#show interfaces fa0/14 switchport
Name: Fa0/14
Switchport: Enabled Administrative Mode: trunk Operational Mode: trunk
Administrative Trunking Encapsulation: dot1q
Operational Trunking Encapsulation: dot1q
We can confirm we have a trunk because the operational mode is “dot1q”.
Let’s try if H1 and H2 can reach each other:
C:\Documents and Settings\H1>ping 192.168.1.2
Pinging 192.168.1.2 with 32 bytes of data:
Reply from 192.168.1.2: bytes=32 time<1ms TTL=128
Reply from 192.168.1.2: bytes=32 time<1ms TTL=128
Reply from 192.168.1.2: bytes=32 time<1ms TTL=128
Reply from 192.168.1.2: bytes=32 time<1ms TTL=128
Ping statistics for 192.168.1.2:
Packets: Sent = 4, Received = 4, Lost = 0 (0% loss),
Approximate round trip times in milli-seconds:
Minimum = 0ms, Maximum = 0ms, Average = 0ms
Excellent! H1 and H2 can reach each other! Does this mean we are
done? Not quite yet…there is more I want to show to you:
SW2#show vlan
VLAN Name Status Ports
---- -------------------------------- --------- -------------------------------
1 default active Fa0/1, Fa0/3, Fa0/4, Fa0/5
Fa0/6, Fa0/7, Fa0/8, Fa0/9
Fa0/10, Fa0/11, Fa0/12, Fa0/13
Fa0/15, Fa0/22, Fa0/23, Fa0/24
Gi0/1, Gi0/2
50 Computers active Fa0/2
First of all, if we use the show vlan command, we don’t see the Fa0/14 interface. This is completely normal because the show vlan command only shows interfaces in access mode and no trunk interfaces.
SW2#show interface fa0/14 trunk Port Mode Encapsulation Status Native vlan Fa0/14 on 802.1q trunking 1 Port Vlans allowed on trunk Fa0/14 1-4094 Port Vlans allowed and active in management domain Fa0/14 1,50 Port Vlans in spanning tree forwarding state and not pruned Fa0/14 50
The show interface trunk command is useful. You can see if an interface is in trunk mode, which trunk encapsulation protocol it uses (802.1Q or ISL), and what the native VLAN is. We can also see that VLANs 1 – 4094 are allowed on this trunk.
We can also see that only VLAN 1 (native VLAN) and VLAN 50 are currently active. Last but not least, you can see which VLANs are in the forwarding state for spanning tree.
I want to show you one more thing about access and trunk interfaces:
SW2#show interface fa0/2 switchport
Name: Fa0/2
Switchport: Enabled
Administrative Mode: static access
Operational Mode: static access
An interface can be in access mode or in trunk mode. The interface above is connected to H2, and you can see that the operational mode is “static access,” which means it’s in access mode.
SW2#show interfaces fa0/14 switchport
Name: Fa0/14
Switchport: Enabled
Administrative Mode: trunk
Operational Mode: trunk
This is our trunk interface which is connected to SW1. You can see the operational mode is trunk mode.
SW2(config-if)#switchport mode ?
access Set trunking mode to ACCESS unconditionally
dot1q-tunnel set trunking mode to TUNNEL unconditionally
dynamic Set trunking mode to dynamically negotiate access or trunk
private-vlan Set private-vlan mode
trunk Set trunking mode to TRUNK unconditionally
If I go to the interface configuration to change the switchport mode, you can see I have more options than access or trunk mode. There is also a dynamic method. Don’t worry about the other options for now.
SW2(config-if)#switchport mode dynamic ? auto Set trunking mode dynamic negotiation parameter to AUTO desirable Set trunking mode dynamic negotiation parameter to DESIRABLE
We can choose between dynamic auto and dynamic desirable. Our switch will automatically determine if the interface should become access or trunk port. So what’s the difference between dynamic auto and dynamic desirable? Let’s find out!
I’m going to play with the switchport mode on SW1 and SW2, and we’ll see the result.



You have a very unique way of explaining, Clear and direct to the point. I am very grateful.
Thank you
I really appreciate your efforts
Hi ,
Im following you LAB but i would like to know how to change the Operational Mode
status .
Every times i would like to change it , it doesn’t work .
#sh int Fa0/21 switchport
Name: Fa0/21
Switchport: Enabled
Administrative Mode: trunk
Operational Mode: down <—
Administrative Trunking Encapsulation: dot1q
Negotiation of Trunking: Off
Access Mode VLAN: 50 (TesteIMO(NOTOUCH))
Trunking Native Mode VLAN: 1 (default)
Voice VLAN: none
Thanks for your help .
Can u check whether u made it no shut?
Please clarify how to interpret the table you listed in the page below with different modes