Root Guard will make sure you don’t accept a certain switch as a root bridge. BPDUs are sent and processed normally but if a switch suddenly sends a BPDU with a superior bridge ID you won’t accept it as the root bridge. Normally SW2 would become the root bridge because it has the best bridge ID, fortunately we have Root Guard on SW3 so it’s not going to happen!
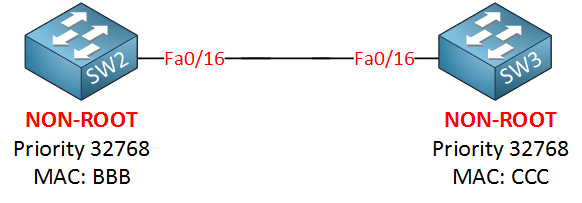
Let me demonstrate this with the following topology:
Let me show you the configuration by using SW2 and SW3, first I will make sure that SW3 is NOT the root bridge:
SW2(config)#spanning-tree vlan 1 priority 4096Now we’ll enable root guard on SW2:
SW2(config)#interface fa0/16
SW2(config-if)#spanning-tree guard root
%SPANTREE-2-ROOTGUARD_CONFIG_CHANGE: Root guard enabled on port FastEthernet0/16.We get a nice notification message that it has been enabled. Let’s enable a debug so we can see what is going on:
SW2#debug spanning-tree events
Spanning Tree event debugging is onNow we’ll upset SW2 by changing the priority to the lowest value possible (0) on SW3. Normally it should now become the root bridge:



Hi Rene,
Simple and short explanation makes very easy to understand . One small question..?
Since Root bridge is specific to Switch , Is there any command to enable the Root guard globally ?
If No, We have to enable the “spanning-tree guard root” in all the Designated Ports of Root bridge to make it always root.
Please correct me If I misunderstood the concept here.
Thanks,
Srini
Hi Srini,
Root guard is always enabled per interface. Each switch will always elect one interface as its root port (unless the switch is the root bridge). The only thing this command does is ensuring that an interface can never become the root port.
Rene
Thanks!
-Srini
Rene,
Hi. Couple questions.
-
-
... Continue reading in our forumI have seen some documents out there that recommend or advise to enable “root guard” on ports connected to end hosts at an access layer switch. Is there any value to still configure root guard if have those end host ports on the access layer switch configured with BPDU-guard & portfast?
I see where you advise above to configure rootguard on distribution or core layer switches - if I have a “V” design as indicated below, is there still any value of configuring root guard on the designated port of Switch 1 and the root port of Swit
Drawing didn’t turn out very well essentially I don’t have a link between SW1 and SW2 and all communication between those switches is via/through switch 3.