Lesson Contents
MST (Multiple Spanning Tree) and PVST+ (Per VLAN Spanning Tree) both offer loop-free layer two topologies but they each use a different approach:
- MST maps multiple VLANs to an instance, reducing the number of spanning tree instances.
- PVST+ calculates an instance for each spanning tree instance.
The two versions are compatible, but how should the two behave on the link that connects the two spanning tree protocols?
PVST+ sends BPDUs for each instance/VLAN, so you could let MST process each BPDU separately with the instance that is configured for the VLAN. MST, however, doesn’t have an instance for each VLAN, so what kind of BPDUs should it send?
This is an issue. Two VLANs may share the same MST instance but use different root bridges, root ports, and other attributes in the PVST+ domain. Which information should MST send in its BPDUs? Creating a 1:1 mapping between the MST and PVST+ information is impossible.
Instead, when an MST region is connected to a PVST+ topology, MST will simulate PVST+ with a feature called the PVST simulation mechanism. What it does is that the MST region will send PVST+ BPDUs (one for each VLAN) on the interfaces that are connected to PVST+ switches. These BPDUs all carry the same information and advertise the same root bridge. The interfaces that connect to the PVST+ topology are called boundary interfaces/ports.
Since PVST+ switches now receive BPDUs for each VLAN from MST carrying the same information, they will all make the same decisions when selecting a root bridge, root port, etc.
Where does the information MST advertises in the simulated PVST+ BPDUs come from? All MST switches have to agree on the same information, so we use the information from the IST for this. The root bridge in the MST region, elected as the root bridge for the IST, will also be used in the PVST+ BPDUs that the PVST simulation uses.
What about the other way around? From PVST+ to MST?
MST decides the port role (root, designated, non-designated) for the boundary interface for all VLANs only by looking at the information in the VLAN 1 BPDU.
Deciding the port role on the boundary interface for all VLANs is risky…after all, it means that we assume that all VLANs use the same root bridge, root ports, etc. We don’t know if the PVST+ domain agrees on the port role for all VLANs we select on our MST boundary interface. However, there are some simple checks that MST can use to determine if PVST+ agrees on the port roles. Let’s take a look at each possible port role.
Designated Port
Suppose MST wants to use the boundary as a designated port. It uses the following check:
MST BPDU from IST must be superior compared to each PVST+ BPDU from every VLAN that you receive on the boundary interface.So, MST compares its IST BPDU to all PVST+ BPDUs (one for each VLAN). If its own BPDU is superior, it knows that PVST+ agrees on the port role, and we can safely turn the boundary interface into a designated port. If not, we know that PVST+ doesn’t agree on our port role, and we block our boundary interface. The status of the interface shows up as broken.
Root Port
The boundary interface can become a root port if the VLAN 1 BPDU it receives is the best BPDU that it gets on any of its boundary interfaces. This means that the root bridge for VLAN 1 is located in the PVST+ domain. When this happens, the interface will go into the forwarding state for all VLANs. This is a tricky situation. MST acts as if all VLANs have their root bridge in the PVST+ domain and turns its boundary interface into the root port for all VLANs, but that might not be the case. To counter this, MST uses the following check:
PVST+ BPDUs for all VLANs except VLAN 1 must be identical or superior compared to the PVST+ VLAN 1 BPDU.This means that MST listens to all PVST+ BPDUs that it receives on its boundary interface and checks if those BPDUs are superior to the VLAN 1 BPDU from PVST+. If so, MST can safely turn its boundary interface into a root port. If not, the switch reports an inconsistency error; the interface will be blocked and show the broken state.
One caveat is that PVST+ uses the system ID extension, which uses the VLAN number as part of the bridge ID. This makes it impossible to have PVST+ BPDUs from different VLANs with identical values. Because of this, PVST+ BPDUs require a priority of at least 4096 lower than the PVST+ VLAN 1 BPDU.
Non-designated Port
Last but not least, the boundary interface could be a non-designated port. It becomes a non-designated port if the boundary interface receives a VLAN 1 PVST+ BPDU superior to its own MST IST BPDU but not good enough to become a root port. In this case, the boundary interface becomes a non-designated port for all VLANs. MST has to check if the PVST+ domain also thinks this should be a non-designated port, and it can quickly check this by listening to all PVST+ BPDUs. When the PVST+ BPDUs are superior to its own BPDU, it can become a non-designated port. Cisco switches don’t do any additional checks. Even if a superior BPDU were received, it would report a PVST inconsistency error, and the port would go into broken mode, but since it’s blocked anyway, it doesn’t matter.
It is easiest to configure your network so that the MST region is the root bridge in your network. If your PVST+ domain has the root bridge, then MST will use the same root port for all VLANs. If the root bridge is in your MST region, then you change the cost per VLAN on your PVST+ switches to use different root ports and a bit of load balancing.
Configuration
Let’s take a look at all of this in action. There are three switches I use:
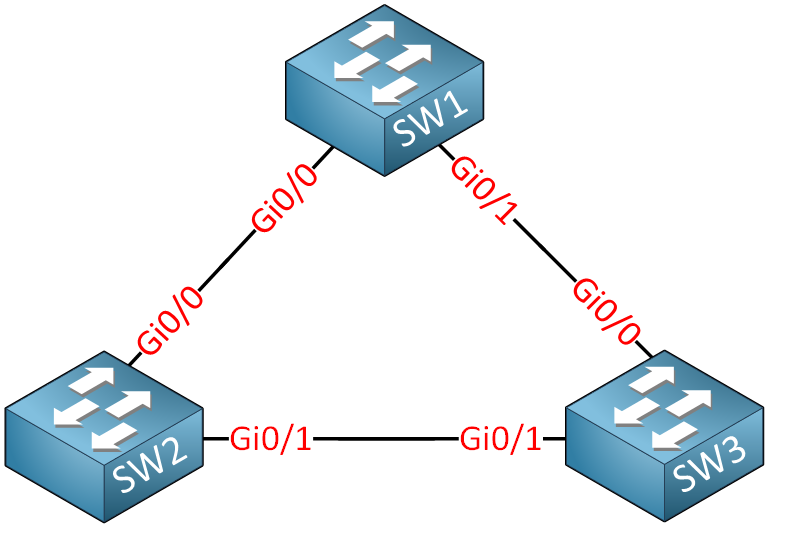
SW1 will use rapid spanning tree.SW2 and SW3 will use MST. We will use three MST instances and six VLANs. Let’s start by configuring the interfaces as trunks and adding some VLANs:
SW1, SW2, & SW3
(config)#interface range GigabitEthernet 0/0 - 1
(config-if-range)#switchport trunk encapsulation dot1q
(config-if-range)#switchport mode trunkSW1, SW2 & SW3
(config)#vlan 10
(config-vlan)#vlan 20
(config-vlan)#exitWe now have a basic configuration that we can use.
MST Root Bridge
In the first scenario, I will use the MST region as the root bridge.
The VLANs are mapped like this:
- VLAN 10 is mapped to instance 1.
- VLAN 20 is mapped to instance 2.
SW2 is the root bridge for instances 0 and 1:
SW2(config)#spanning-tree mode mst
SW2(config)#spanning-tree mst configuration
SW2(config-mst)#name REGION1
SW2(config-mst)#instance 1 vlan 10
SW2(config-mst)#instance 2 vlan 20SW2(config)#spanning-tree mst 0-1 priority 8192SW3 will become the root bridge for instance 2:
SW3(config)#spanning-tree mode mst
SW3(config)#spanning-tree mst configuration
SW3(config-mst)#name REGION1
SW3(config-mst)#instance 1 vlan 10
SW3(config-mst)#instance 2 vlan 20SW3(config-mst)#spanning-tree mst 2 priority 8192SW1 is running rapid spanning tree with its default priority.
Configurations
Want to take a look for yourself? Here you will find the startup configuration of each device.
SW1
hostname SW1
!
spanning-tree mode pvst
spanning-tree vlan 1 priority 4096
spanning-tree vlan 10,20 priority 0
!
interface GigabitEthernet0/0
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet0/1
switchport trunk encapsulation dot1q
switchport mode trunk
!
endSW2
hostname SW2
!
ip cef
!
spanning-tree mode mst
!
spanning-tree mst configuration
name REGION1
instance 1 vlan 10
instance 2 vlan 20
!
spanning-tree mst 0-1 priority 8192
!
interface GigabitEthernet0/0
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet0/1
switchport trunk encapsulation dot1q
switchport mode trunk
!
endSW3
hostname SW3
!
ip cef
!
spanning-tree mode mst
!
spanning-tree mst configuration
name REGION1
instance 1 vlan 10
instance 2 vlan 20
!
spanning-tree mst 2 priority 8192
!
interface GigabitEthernet0/0
switchport trunk encapsulation dot1q
switchport mode trunk
!
interface GigabitEthernet0/1
switchport trunk encapsulation dot1q
switchport mode trunk
!
endHere’s what all switches think of the topology:
SW1#show spanning-tree vlan 1
VLAN0001
Spanning tree enabled protocol ieee
Root ID Priority 8192
Address 5254.0016.8d33
Cost 4
Port 1 (GigabitEthernet0/0)
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Bridge ID Priority 32769 (priority 32768 sys-id-ext 1)
Address 5254.000d.0b6c
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Aging Time 15 sec
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi0/0 Root FWD 4 128.1 P2p
Gi0/1 Altn BLK 4 128.2 P2pSW1#show spanning-tree vlan 10
VLAN0010
Spanning tree enabled protocol ieee
Root ID Priority 8192
Address 5254.0016.8d33
Cost 4
Port 1 (GigabitEthernet0/0)
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Bridge ID Priority 32778 (priority 32768 sys-id-ext 10)
Address 5254.000d.0b6c
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Aging Time 15 sec
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi0/0 Root FWD 4 128.1 P2p
Gi0/1 Altn BLK 4 128.2 P2pSW1#show spanning-tree vlan 20
VLAN0020
Spanning tree enabled protocol ieee
Root ID Priority 8192
Address 5254.0016.8d33
Cost 4
Port 1 (GigabitEthernet0/0)
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Bridge ID Priority 32788 (priority 32768 sys-id-ext 20)
Address 5254.000d.0b6c
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Aging Time 15 sec
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi0/0 Root FWD 4 128.1 P2p
Gi0/1 Altn BLK 4 128.2 P2pThe output above is interesting to see. As explained earlier, MST maps all VLANs to the IST, so even VLAN 20 shares the same information, even though SW3 is the root bridge for VLAN 20. SW1 sees SW2 as the root bridge for all VLANs.
Here is SW2:
SW2#show spanning-tree mst 0
##### MST0 vlans mapped: 1-9,11-19,21-4094
Bridge address 5254.0016.8d33 priority 8192 (8192 sysid 0)
Root this switch for the CIST
Operational hello time 2 , forward delay 15, max age 20, txholdcount 6
Configured hello time 2 , forward delay 15, max age 20, max hops 20
Interface Role Sts Cost Prio.Nbr Type
---------------- ---- --- --------- -------- --------------------------------
Gi0/0 Desg FWD 20000 128.1 P2p Bound(PVST)
Gi0/1 Desg FWD 20000 128.2 P2pSW2#show spanning-tree mst 1
##### MST1 vlans mapped: 10
Bridge address 5254.0016.8d33 priority 8193 (8192 sysid 1)
Root this switch for MST1
Interface Role Sts Cost Prio.Nbr Type
---------------- ---- --- --------- -------- --------------------------------
Gi0/0 Desg FWD 20000 128.1 P2p Bound(PVST)
Gi0/1 Desg FWD 20000 128.2 P2pSW2#show spanning-tree mst 2
##### MST2 vlans mapped: 20
Bridge address 5254.0016.8d33 priority 32770 (32768 sysid 2)
Root address 5254.001d.738f priority 8194 (8192 sysid 2)
port Gi0/1 cost 20000 rem hops 19
Interface Role Sts Cost Prio.Nbr Type
---------------- ---- --- --------- -------- --------------------------------
Gi0/0 Desg FWD 20000 128.1 P2p Bound(PVST)
Gi0/1 Root FWD 20000 128.2 P2pSW2 is the root bridge for the CIST (instance 0) and instance 1. Here is SW3:
SW3#show spanning-tree mst 0
##### MST0 vlans mapped: 1-9,11-19,21-4094
Bridge address 5254.001d.738f priority 32768 (32768 sysid 0)
Root address 5254.0016.8d33 priority 8192 (8192 sysid 0)
port Gi0/1 path cost 0
Regional Root address 5254.0016.8d33 priority 8192 (8192 sysid 0)
internal cost 20000 rem hops 19
Operational hello time 2 , forward delay 15, max age 20, txholdcount 6
Configured hello time 2 , forward delay 15, max age 20, max hops 20
Interface Role Sts Cost Prio.Nbr Type
---------------- ---- --- --------- -------- --------------------------------
Gi0/0 Desg FWD 20000 128.1 P2p Bound(PVST)
Gi0/1 Root FWD 20000 128.2 P2pSW3#show spanning-tree mst 1
##### MST1 vlans mapped: 10
Bridge address 5254.001d.738f priority 32769 (32768 sysid 1)
Root address 5254.0016.8d33 priority 8193 (8192 sysid 1)
port Gi0/1 cost 20000 rem hops 19
Interface Role Sts Cost Prio.Nbr Type
---------------- ---- --- --------- -------- --------------------------------
Gi0/0 Desg FWD 20000 128.1 P2p Bound(PVST)
Gi0/1 Root FWD 20000 128.2 P2pSW3#show spanning-tree mst 2
##### MST2 vlans mapped: 20
Bridge address 5254.001d.738f priority 8194 (8192 sysid 2)
Root this switch for MST2
Interface Role Sts Cost Prio.Nbr Type
---------------- ---- --- --------- -------- --------------------------------
Gi0/0 Desg FWD 20000 128.1 P2p Bound(PVST)
Gi0/1 Desg FWD 20000 128.2 P2pSW3 sees SW2 as the root bridge and regional root bridge for instance 0. SW3 also sees SW2 as the root bridge for instance 1. SW3 is the root bridge for instance 2.
Let’s see what happens now when I try to make SW1 the new root bridge for one VLAN:
SW1(config)#spanning-tree vlan 20 priority 4096As soon as you do this, this message will show up on SW2 and SW3:
SW2#
%SPANTREE-2-PVSTSIM_FAIL: Blocking designated port Gi0/0: Inconsistent superior PVST BPDU received on VLAN 20, claiming root 4116:5254.000d.0b6cSW3#
%SPANTREE-2-PVSTSIM_FAIL: Blocking designated port Gi0/0: Inconsistent superior PVST BPDU received on VLAN 20, claiming root 4116:5254.000d.0b6cThe spanning tree PVST simulation fails. For the boundary interface to be a designated port, the MST IST BPDU must be superior compared to all PVST+ BPDUs, which is not the case now. As a result, the boundary interface is now in the broken state on SW2:
SW2#show spanning-tree mst 0
##### MST0 vlans mapped: 1-9,11-19,21-29,31-39,41-49,51-59,61-4094
Bridge address 5254.0016.8d33 priority 8192 (8192 sysid 0)
Root this switch for the CIST
Operational hello time 2 , forward delay 15, max age 20, txholdcount 6
Configured hello time 2 , forward delay 15, max age 20, max hops 20
Interface Role Sts Cost Prio.Nbr Type
---------------- ---- --- --------- -------- --------------------------------
Gi0/0 Desg BKN*20000 128.1 P2p Bound(PVST) *PVST_Inc
Gi0/1 Desg FWD 20000 128.2 P2pSW2#show spanning-tree mst 1
##### MST1 vlans mapped: 10,20,30
Bridge address 5254.0016.8d33 priority 8193 (8192 sysid 1)
Root this switch for MST1
Interface Role Sts Cost Prio.Nbr Type
---------------- ---- --- --------- -------- --------------------------------
Gi0/0 Desg BKN*20000 128.1 P2p Bound(PVST) *PVST_Inc
Gi0/1 Desg FWD 20000 128.2 P2pSW2#show spanning-tree mst 2
##### MST2 vlans mapped: 40,50,60
Bridge address 5254.0016.8d33 priority 32770 (32768 sysid 2)
Root address 5254.001d.738f priority 8194 (8192 sysid 2)
port Gi0/1 cost 20000 rem hops 19
Interface Role Sts Cost Prio.Nbr Type
---------------- ---- --- --------- -------- --------------------------------
Gi0/0 Desg BKN*20000 128.1 P2p Bound(PVST) *PVST_Inc
Gi0/1 Root FWD 20000 128.2 P2pAnd also on SW3:
SW3#show spanning-tree mst 0
##### MST0 vlans mapped: 1-9,11-19,21-4094
Bridge address 5254.001d.738f priority 32768 (32768 sysid 0)
Root address 5254.0016.8d33 priority 8192 (8192 sysid 0)
port Gi0/1 path cost 0
Regional Root address 5254.0016.8d33 priority 8192 (8192 sysid 0)
internal cost 20000 rem hops 19
Operational hello time 2 , forward delay 15, max age 20, txholdcount 6
Configured hello time 2 , forward delay 15, max age 20, max hops 20
Interface Role Sts Cost Prio.Nbr Type
---------------- ---- --- --------- -------- --------------------------------
Gi0/0 Desg BKN*20000 128.1 P2p Bound(PVST) *PVST_Inc
Gi0/1 Root FWD 20000 128.2 P2pSW3#show spanning-tree mst 1
##### MST1 vlans mapped: 10
Bridge address 5254.001d.738f priority 32769 (32768 sysid 1)
Root address 5254.0016.8d33 priority 8193 (8192 sysid 1)
port Gi0/1 cost 20000 rem hops 19
Interface Role Sts Cost Prio.Nbr Type
---------------- ---- --- --------- -------- --------------------------------
Gi0/0 Desg BKN*20000 128.1 P2p Bound(PVST) *PVST_Inc
Gi0/1 Root FWD 20000 128.2 P2pSW3#show spanning-tree mst 2
##### MST2 vlans mapped: 20
Bridge address 5254.001d.738f priority 8194 (8192 sysid 2)
Root this switch for MST2
Interface Role Sts Cost Prio.Nbr Type
---------------- ---- --- --------- -------- --------------------------------
Gi0/0 Desg BKN*20000 128.1 P2p Bound(PVST) *PVST_Inc
Gi0/1 Desg FWD 20000 128.2 P2pThe GigabitEthernet 0/0 interface enters the BKN (broken) status for all instances/VLANs. In the last output, you can see that even though GigabitEthernet 0/0 is in the broken state, SW2 does recognize SW1 as the root bridge.
Let’s increase the priority of SW1 so that SW2 and SW3 become the root bridges in this topology.
SW1(config)#spanning-tree vlan 20 priority 32768This solves our issues with the broken interfaces:
SW2#
%SPANTREE-2-PVSTSIM_OK: PVST Simulation inconsistency cleared on port GigabitEthernet0/0.SW3#
%SPANTREE-2-PVSTSIM_OK: PVST Simulation inconsistency cleared on port GigabitEthernet0/0.SW1 now sees the MST region as the root bridge. The inconsistency is cleared since all PVST+ BPDUs that SW2 and SW3 receive are inferior to the MST IST BPDU.
Having the MST region as the root bridge is a best practice. It’s simple to maintain, and it allows load balancing. For example, let’s say we want the PVST+ domain to use another root port for VLAN 20. We can achieve this by playing with the cost:
SW1(config)#interface GigabitEthernet 0/1
SW1(config-if)#spanning-tree vlan 20 cost 1SW1 now uses GigabitEthernet 0/1 as its root port to reach VLAN 60:
SW1#show spanning-tree vlan 20
VLAN0020
Spanning tree enabled protocol ieee
Root ID Priority 8192
Address 5254.0016.8d33
Cost 1
Port 2 (GigabitEthernet0/1)
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Bridge ID Priority 32788 (priority 32768 sys-id-ext 20)
Address 5254.000d.0b6c
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Aging Time 15 sec
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi0/0 Altn BLK 4 128.1 P2p
Gi0/1 Root FWD 1 128.2 P2pGigabitEthernet 0/1 is now the root port for VLAN 20. All other VLANs still use GigabitEthernet 0/0 as their root port:
SW1#show spanning-tree vlan 1
VLAN0001
Spanning tree enabled protocol ieee
Root ID Priority 8192
Address 5254.0016.8d33
Cost 4
Port 1 (GigabitEthernet0/0)
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Bridge ID Priority 32769 (priority 32768 sys-id-ext 1)
Address 5254.000d.0b6c
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Aging Time 300 sec
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi0/0 Root FWD 4 128.1 P2p
Gi0/1 Altn BLK 4 128.2 P2pSW1#show spanning-tree vlan 10
VLAN0010
Spanning tree enabled protocol ieee
Root ID Priority 8192
Address 5254.0016.8d33
Cost 4
Port 1 (GigabitEthernet0/0)
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Bridge ID Priority 32778 (priority 32768 sys-id-ext 10)
Address 5254.000d.0b6c
Hello Time 2 sec Max Age 20 sec Forward Delay 15 sec
Aging Time 300 sec
Interface Role Sts Cost Prio.Nbr Type
------------------- ---- --- --------- -------- --------------------------------
Gi0/0 Root FWD 4 128.1 P2p
Gi0/1 Altn BLK 4 128.2 P2pPVST+ Root Bridge
It is possible to have the root bridge in the PVST+ domain.
Let’s see how we can make this work. I’ll make SW1 the root bridge for VLAN 1:


Hello Stefano.
PVST+ as its name suggests creates an spanning tree instance for EACH VLAN. MST on the other hand can have many VLANs participate in a single spanning tree instance thus reducing the number of spanning tree instances and thus consuming fewer system resources (CPU, Memory etc).
I hope this has been helpful!
Laz
Hello Ehsan
Essentially, PVRST uses multiple instances of IEEE 802.1w. Most non-cisco devices that support RSTP will support one instance of PVRST. In most cases, because PVRST is backward compatible with RSTP, the PVRST implementation will revert to RSTP. So you are essentially correct in your descsription.
I hope this has been helpful!
Laz
Thank you very much Lazaros!
Hi Rene,
In the video example, why did SW3 choose to have SW2 as its root where SW1 in the PVST+ is root ? Did it have to follow MST root port ?
Thanks,
M
Hello Madhu
Can you please clarify at which point in the video this situation takes place? Also, if the same is found in the lesson text, please specify the location so we can look more closely at it and so that we can respond more appropriately to your question.
Thanks!
Laz