Lesson Contents
Multicast IGMP membership report messages include the multicast group addresses that our receivers want to join. By default, all multicast groups will be accepted. What if we want to restrict this?
It is possible to filter certain multicast groups. We can configure IGMP filtering on a multicast router or on a switch where IGMP snooping is enabled. In this lesson, I’ll show you how to do both.
We will use the following topology for this:
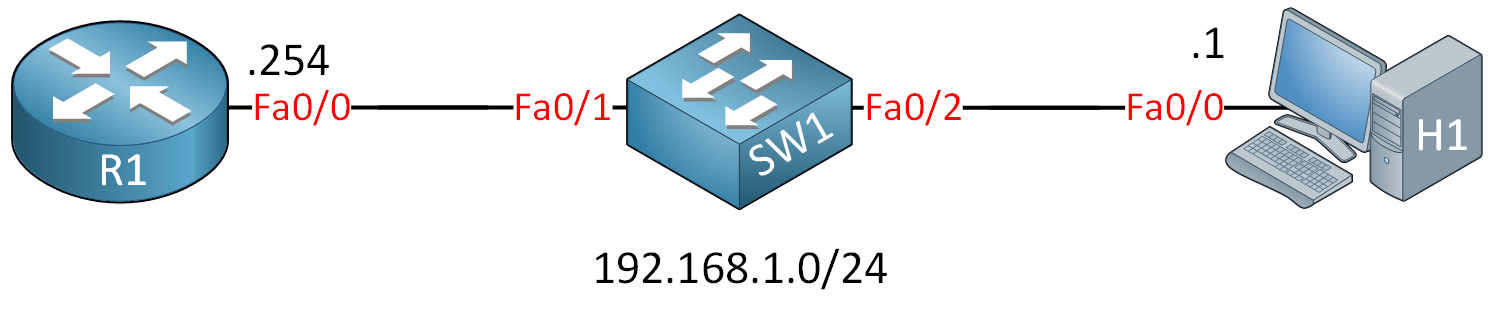
R1 will be our multicast router, SW1 has IGMP snooping enabled and H1 is a multicast receiver.
Configuration
First, let’s enable PIM on R1 so that it processes IGMP traffic:
R1(config)#interface FastEthernet 0/0
R1(config-if)#ip pim sparse-modeAnd let’s enable a debug so we can see IGMP filtering in action:
R1#debug ip igmp
IGMP debugging is onRight now there are no filters. Let’s configure H1 to join a multicast group so that we can see what the debug normally looks like:
H1(config)#interface FastEthernet 0/0
H1(config-if)#ip igmp join-group 239.1.1.1Here’s what we get:
R1#
IGMP(0): Received v2 Report on FastEthernet0/0 from 192.168.1.1 for 239.1.1.1
IGMP(0): Received Group record for group 239.1.1.1, mode 2 from 192.168.1.1 for 0 sources
IGMP(0): WAVL Insert group: 239.1.1.1 interface: FastEthernet0/0SuccessfulR1 receives the membership report for 239.1.1.1 and installs it. We can verify this with the show ip igmp groups command:
R1#show ip igmp groups
IGMP Connected Group Membership
Group Address Interface Uptime Expires Last Reporter Group Accounted
239.1.1.1 FastEthernet0/0 00:00:43 00:02:45 192.168.1.1So far so good…time to filter something!
Router IGMP Filter
Let’s configure our router to filter multicast group 239.2.2.2. We’ll need to create an access-list for this:
R1(config)#ip access-list standard LIMIT_IGMP
R1(config-std-nacl)#deny host 239.2.2.2
R1(config-std-nacl)#permit 224.0.0.0 15.255.255.255The access-list above will deny 239.2.2.2 and permit any other multicast groups. Let’s enable it with the ip igmp access-group command:
R1(config)#interface FastEthernet 0/0
R1(config-if)#ip igmp access-group LIMIT_IGMPNow let’s see what happens when our receiver joins 239.2.2.2:
H1(config)#interface FastEthernet 0/0
H1(config-if)#ip igmp join-group 239.2.2.2Here’s what the router will tell us:
R1#
IGMP(0): Received v2 Report on FastEthernet0/0 from 192.168.1.1 for 239.2.2.2
IGMP(*): Group 239.2.2.2 access denied on FastEthernet0/0As expected, the multicast group is denied. You can also see these matches in the access-list:
R1#show access-lists
Standard IP access list LIMIT_IGMP
10 deny 239.2.2.2 (1 match)
20 permit 224.0.0.0, wildcard bits 15.255.255.255 (1 match)That’s all there is to it.
Switch IGMP Snooping Filter
Let’s see how we can create a filter on the switch. We need to create an IGMP profile for this:
SW1(config)#ip igmp profile 1
SW1(config-igmp-profile)#deny
SW1(config-igmp-profile)#range 239.3.3.3The profile above lets us block multicast group 239.3.3.3. Let’s activate it:
SW1(config)#interface FastEthernet 0/2
SW1(config-if)#ip igmp filter 1 The ip igmp filter command is what we need to activate the IGMP profile. You can activate this on a port, SVI or VLAN.
Let’s see if it works. We’ll enable a debug on the switch:
SW1#
SW1#debug ip igmp filter
IGMP debugging is onLet’s join multicast group 239.3.3.3:
H1(config)#interface FastEthernet 0/0
H1(config-if)#ip igmp join-group 239.3.3.3Here’s what the switch will tell us:
SW1#
IGMPFILTER: igmp_filter_process_pkt(): checking group 239.3.3.3 from Fa0/2: deny
IGMPFILTER: igmp_filter_process_pkt(): checking group 239.2.2.2 from Fa0/2: permitMulticast group 239.3.3.3 is denied, you can see that 239.2.2.2 is still accepted.
Configurations
Want to take a look for yourself? Here you will find the final configuration of each device.


What would be the utility of this in real life?
Hello Stefanio
There are several reasons why we would want to filter IGMP packets. The most basic and important reason is to allow for a network to function more efficiently. The details follow:
IGMP filtering allows users to configure filters on a switch virtual interface (SVI), a per-port, or a per-port per-VLAN basis to control the propagation of IGMP traffic through the network. By managing the IGMP traffic, IGMP filtering provides the capability to manage IGMP snooping, which in turn controls the forwarding of multicast traffic.
When an IGMP packet is re
... Continue reading in our forumHello Rene
I have a simple question about this topic. About Router filter, its only when you want to block from this net to another upstream router, cause i can see if source and destination is in the same net (this example) they can forward traffic normaly or in some way router gives this information to switch to not consider this blocked multicast group. Thnkas for your asnwer.
Jose
Hello Jose
The IGMP filter function can be configured on both a router and a switch. When configured on a router, then yes, only multicast traffic between subnets are filtered. If you want to filter within the same subnet, then switches that have IGMP Snooping Filter capability can filter multicast traffic at ports, VLANs or SVIs.
There is no communication between the router and the switch for such configurations. Each device is configured independently.
I hope this has been helpful!
Laz
Lazaros thanks for your answer!