Lesson Contents
In this lesson, I want to demonstrate to you how to install a user certificate on an Android device so that you can authenticate to a wireless network using EAP-TLS. This is the most secure method of authentication when it comes to wireless networks, but it requires some more effort as you require certificates on the server and each client device.
If you don’t have a RADIUS server and Certificate Authority yet, then you should take a look at my PEAP and EAP-TLS on Windows Server 2008 lesson. In this lesson, I will be using a Windows Server 2008 machine running Certificate Services to generate a client certificate for my Android device.
There are three devices that we require for this lesson:
- Android Device: I’m using my Samsung Galaxy S3 running Android 4.x
- Certificate Authority: required to generate the user certificate. I’m using Windows Server 2008 R2.
- Windows computer: Used to request the user certificate for the Android device. I will be using Windows 7 in my example.
And there are two certificates that we require:
- User certificate.
- Root CA certificate.
The user certificate is required to authenticate the user, and the root CA certificate is required in case you created your own certificate authority. We’ll start with the creation of a user certificate.
Generate User Certificate on Windows 7
First, we will generate a user certificate for the Android device. I will use Windows 7 to connect to the Certificate Authority and request a user certificate. I will use Web enrollment for this as it’s probably the most convenient method of enrolling user certificates.
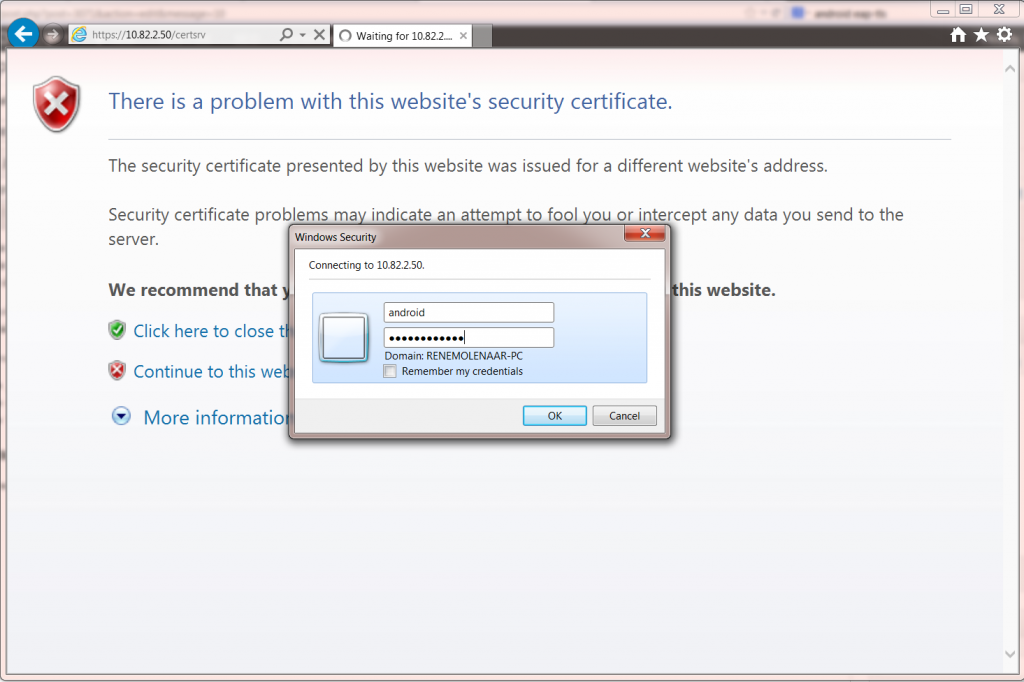
Open the web browser and open http://your-server-ip/certsrv. Enter the credentials of the user account that requires a certificate. I’m doing this for a user called “Android”.
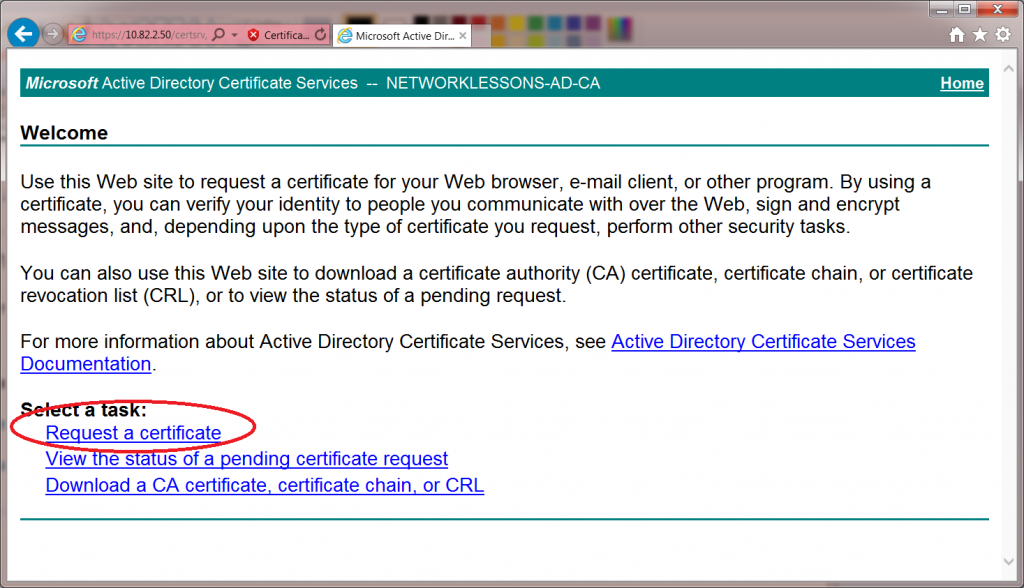
Click on the request a certificate button to continue.
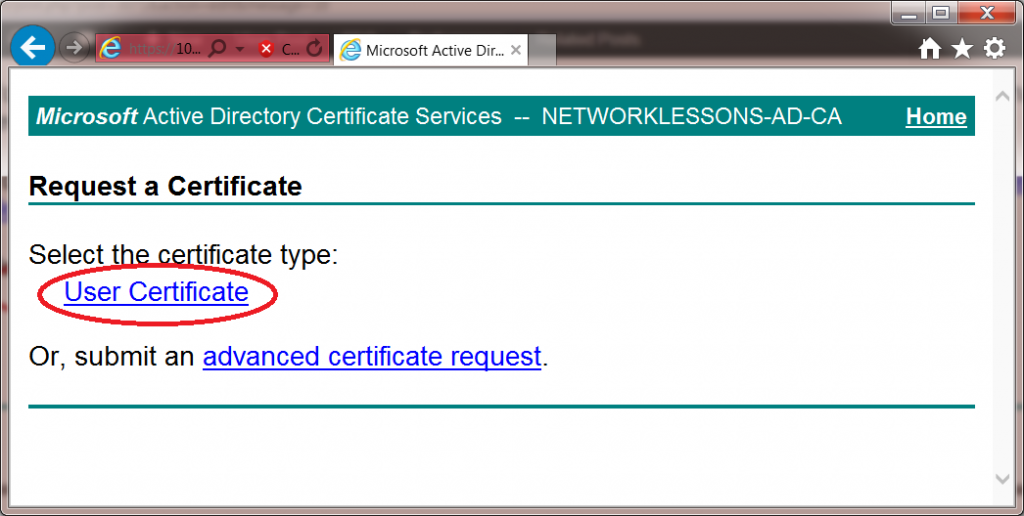
There is no need for advanced options. Click on user certificate to continue.
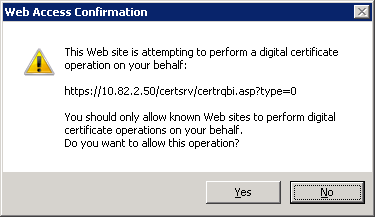
Your web browser will warn you that you are about to request a certificate, click on Yes to continue.
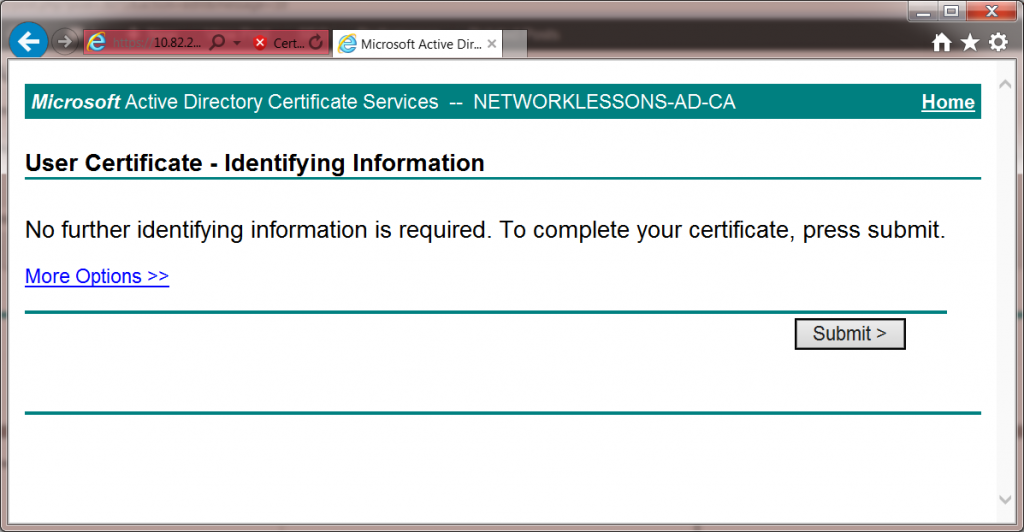
In the final screen, the web enrollment is ready to submit your request. Hit the submit button to continue.
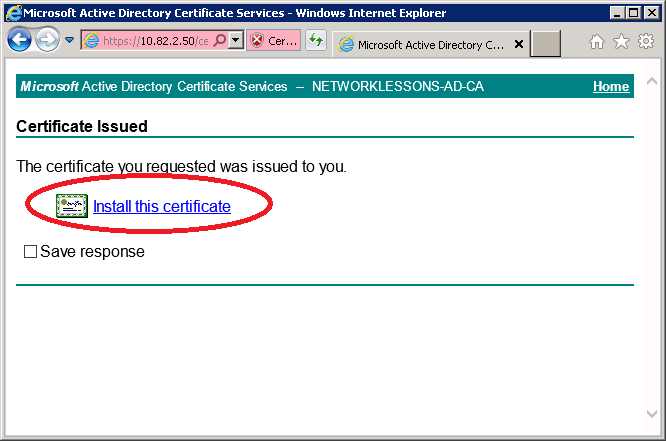
Your user certificate will be ready, and the web browser will ask if it should install the user certificate for you. Click on Install this Certificate to continue.
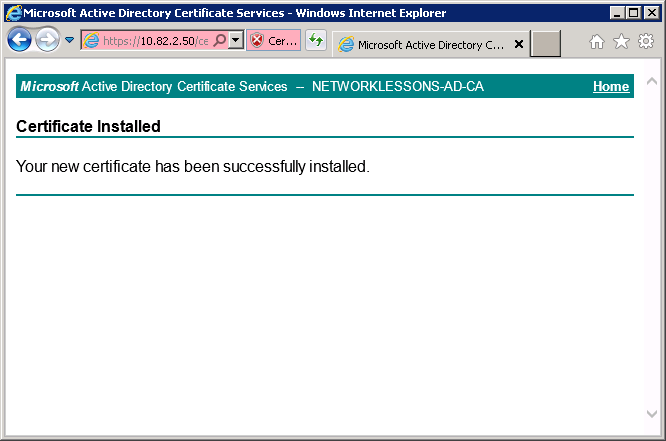
If everything went OK, you should get a message that the user certificate has been installed.
Now we have a user certificate on our Windows 7 computer. We will export this user certificate and import it to our Android device.
Export Certificates
Our Android device will require the user certificate that we just generated but also the root CA certificate in case you are running your own Certificate Authority. I will use my Windows 7 computer to export both certificates. We’ll start with the user certificate…
Export User Certificate
We will use the certificate manager on Windows 7 to view our certificates and export them.
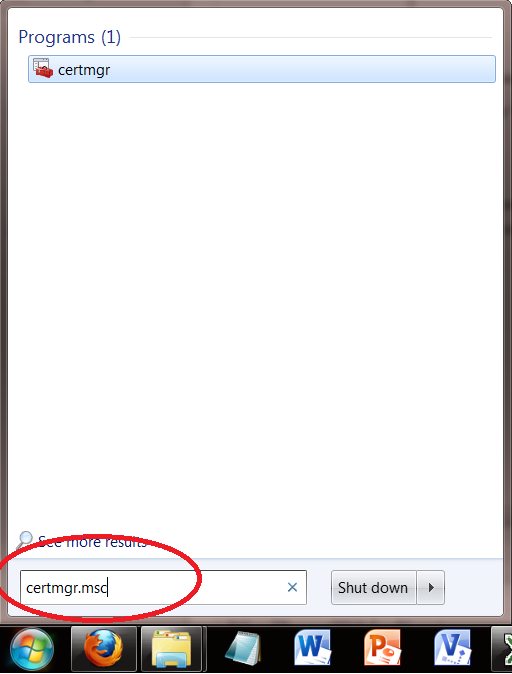
Click on Start > type “CERTMGR.MSC” (without the quotes) and hit enter.
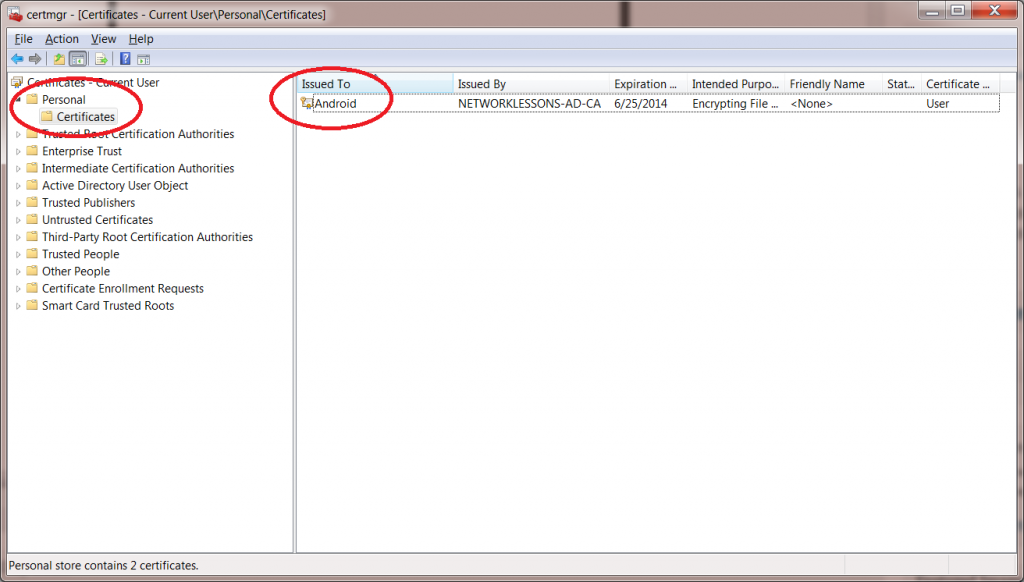
The Certificate manager will start. Click on Personal > Certificates and you will see the user certificate that we generated for the Android user.
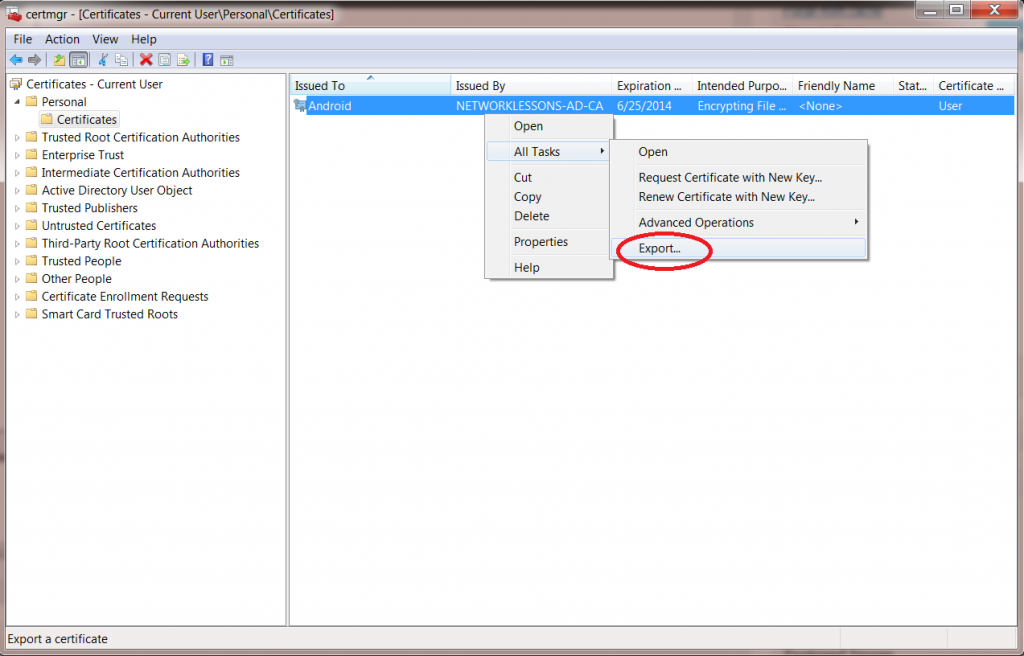
Click on the Android user certificate (right mouse click) and select Export.
You will see the certificate export wizard. Click Next to continue.

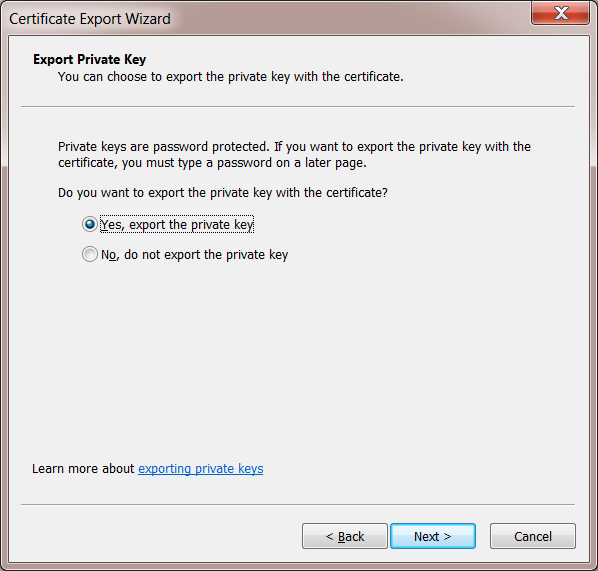
The wizard will ask you to export the private key for the user certificate. Select Yes, export the private key, and click Next to continue.
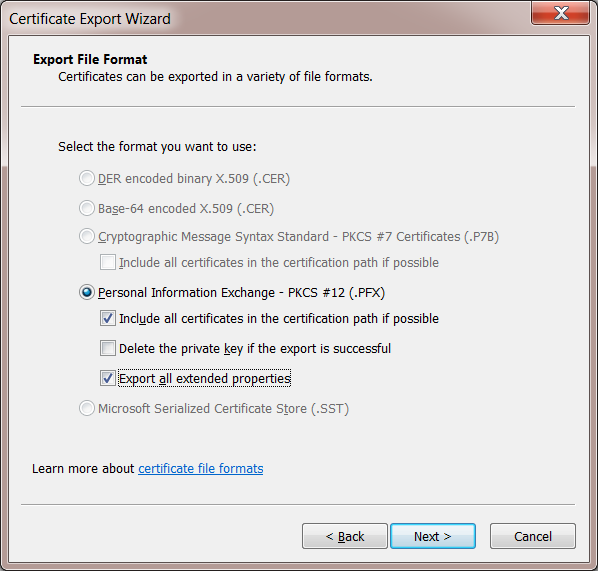
In the next screen, you will have to choose the file format. Everything is greyed out since this is a user certificate. Select the “Include all certificates in the certification path if possible” and “Export all extended properties” checkboxes. Click Next to continue.
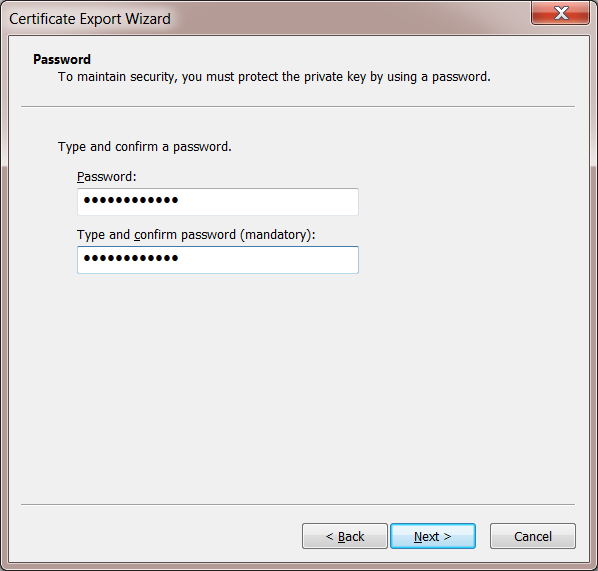
The export wizard will ask you to protect the private key with a password. This is a good idea, so enter a secure password. Click Next to continue.
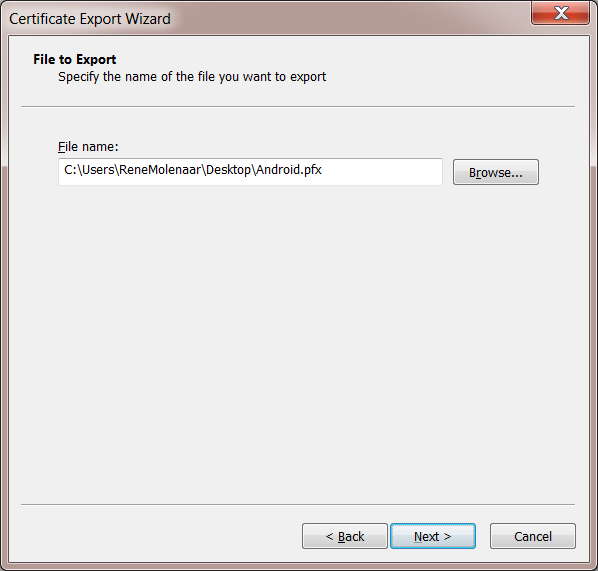
The export wizard will ask you for a filename. I’ll name my user certificate “Android”. Click Next to continue.
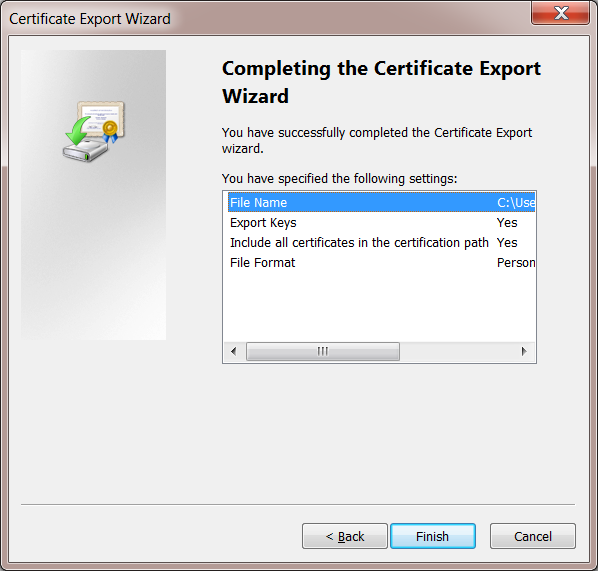
Finally, the export is done. Click Finish to continue.
Now we have the user certificate for user Android stored in a file. We still will need the root CA certificate…
Export Root CA Certificate
If you don’t have the root CA certificate yet, you will have to export it from the certificate authority or your Windows 7 computer. In my other lesson, I already covered how to export the root CA in installing PEAP and EAP-TLS on Windows Server 2008. Take a look at the Configure Wireless Client section to see how you can export the root CA to a filename.
Once you are done, you should have two files:
- The user certificate is in PFX file format.
- The root CA certificate is in DER file format.
We are now ready to import the certificates on our Android device.
Import Certificates on Android Device
Most Android devices will only import certificates from an SD card (internal or external). I am using a Samsung Galaxy S3 running Android 4.x but importing the certificates should be similar on other Android 4.x devices.
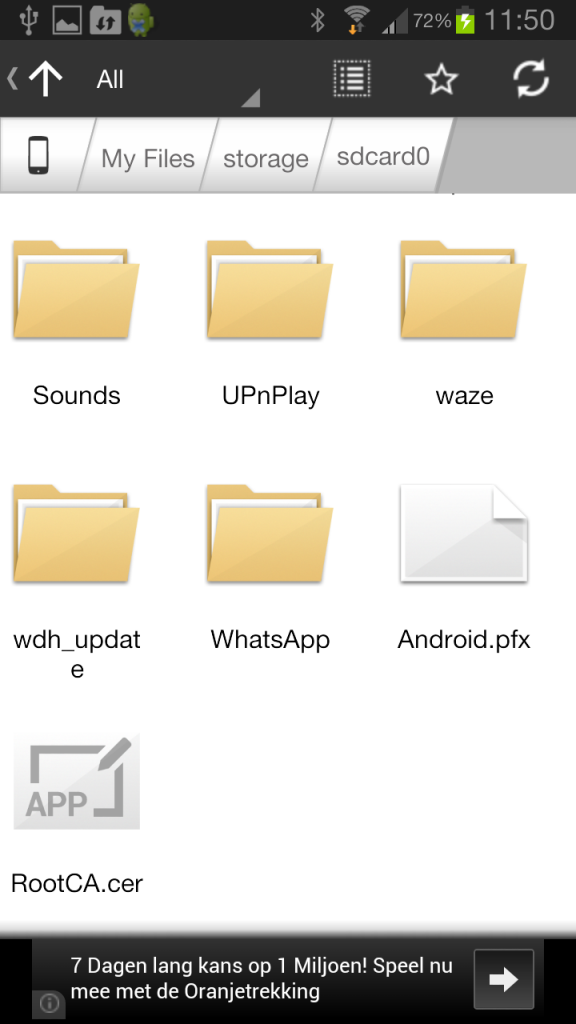
First, you need to copy the two certificate files to your Android device. In my case, I had to copy it to the internal storage, but it’s possible that you need to copy it to an external SD card on other Android devices. Whatever storage “device” it is, you need to copy the files to the root…don’t use any sub-folders. Here’s an example of where I stored the certificate files on my Samsung Galaxy S3:
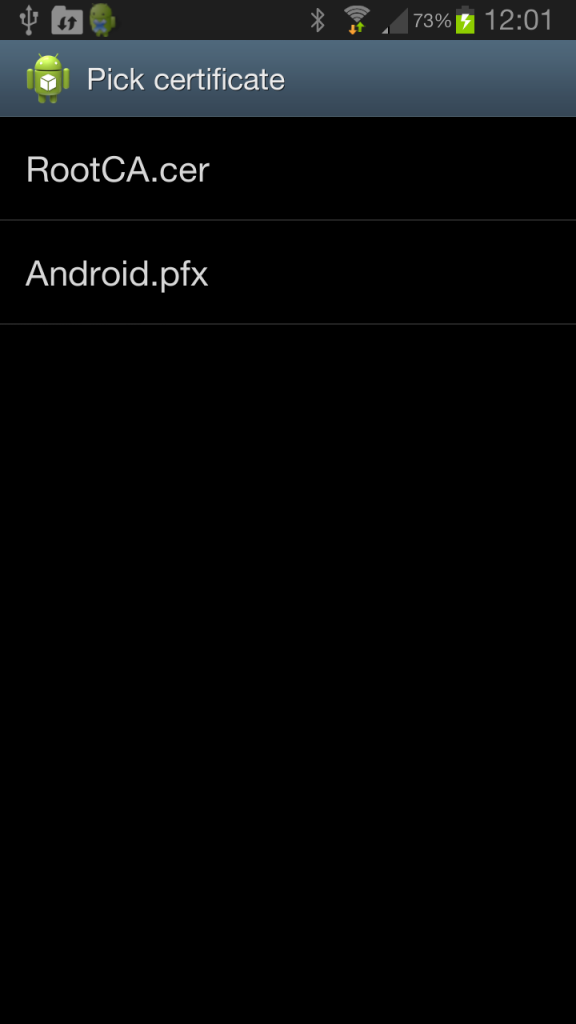
Above, you can see that I stored the following two files on sdcard0 (despite the name, this is the internal storage of the phone):
- Android.pfx (user certificate).
- RootCA.cer (root CA certificate).
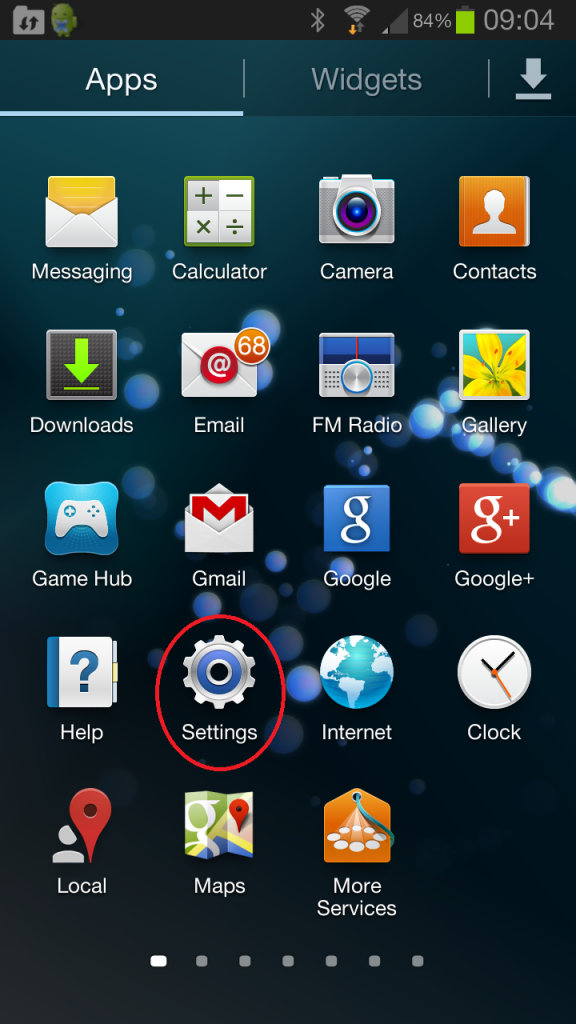
Once you have the files in place, you import them. Go to the settings of your Android device.
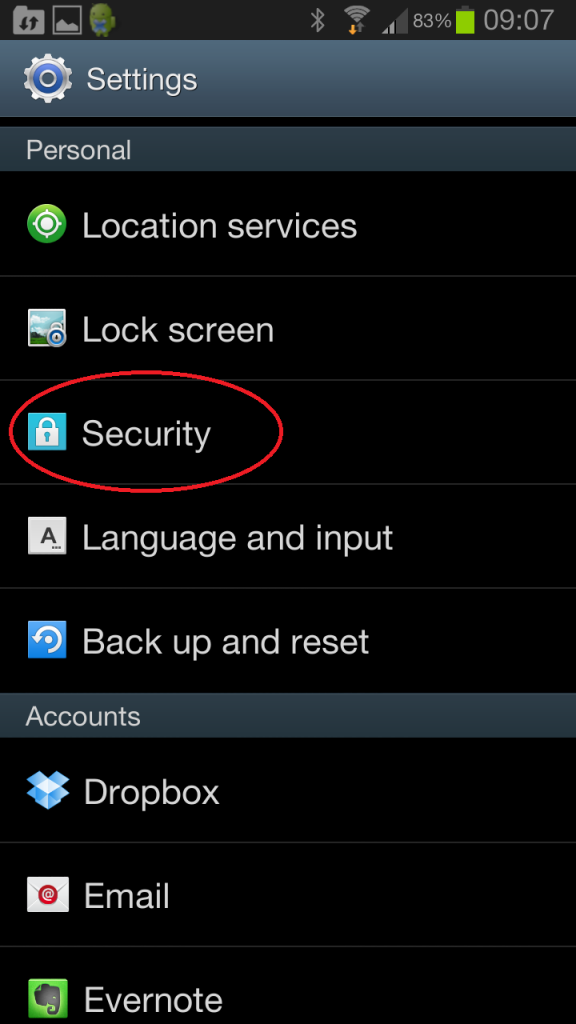
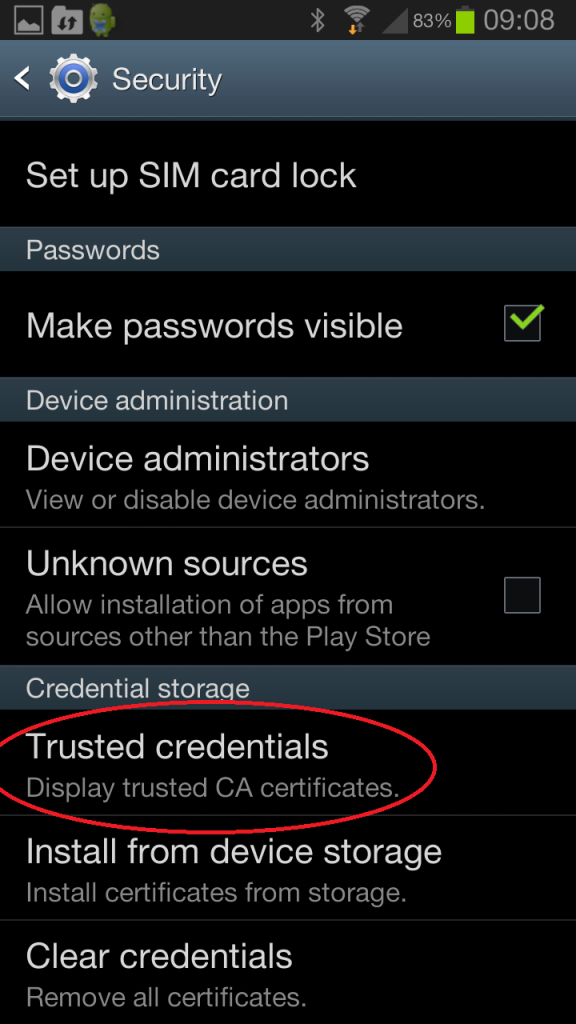
Select the Security option from the Settings menu.
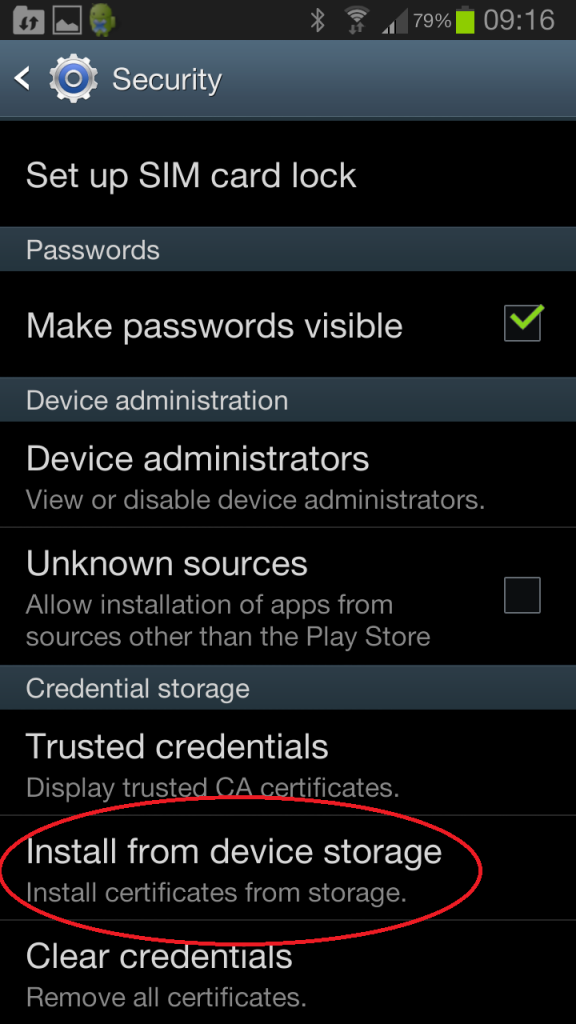
At the bottom, you will find the Credentials storage. Select Install from storage device.
Your Android device will find the certificate files on your storage device and prompt you with the following screen.
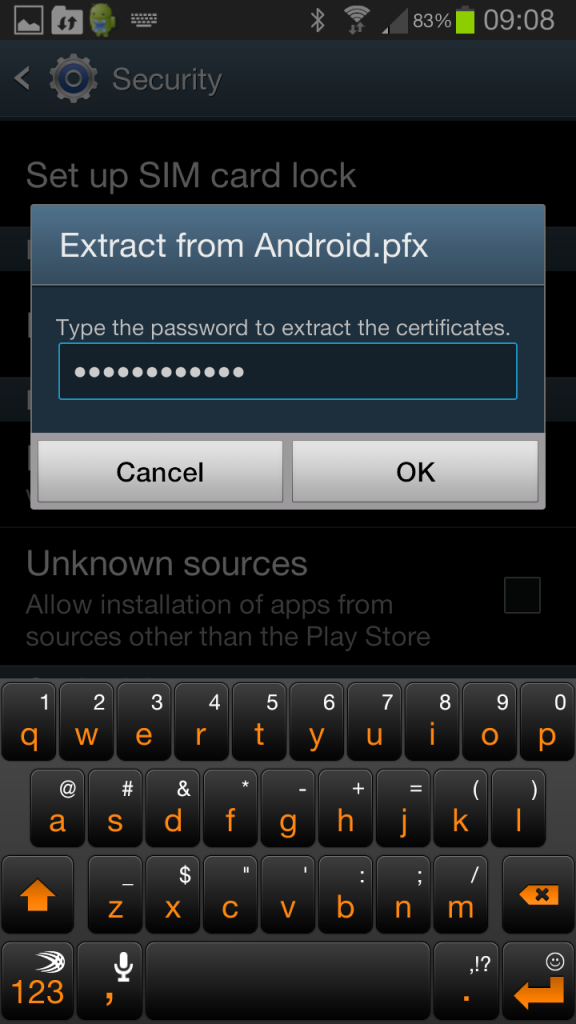
We need to install both. Let me give you an example of the user certificate. Type in the password for the private key and hit OK.
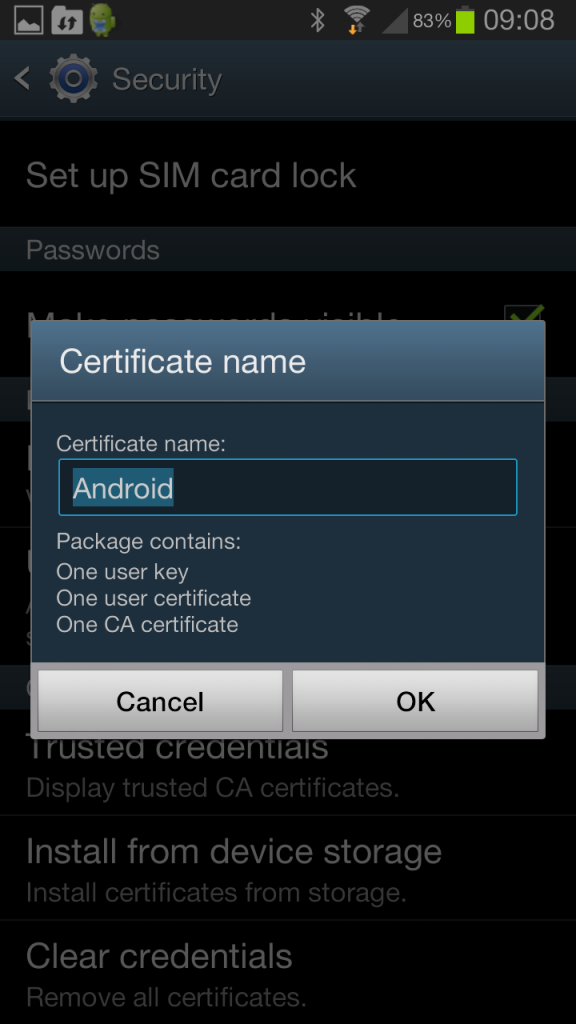
Android will ask you for a certificate name. Keep the default or rename it to something else and press OK.
Make sure you import both certificates. You can verify that your Android device recognizes the certificates. Select Trusted credentials if you want to take a look.
Below you can see that this Android device has a user certificate.


 username
username
Hi. Thanks for the thorough walkthrough. I’m having issues at the point of connecting to the SSID. Once i try to connect, i am presented with an incorrect password error. Subsequent triesare left hanging on a “connecting” message. Have you came across this during your config?
Hi,
Because there are many things to configure there are a lot of things that could go wrong. Your best option is to start looking in the event viewer of server 2008 as it shows you why a client was rejected…
Rene
Hello,
Great post. Very informative. Two questions if I may; EAP-TLS user certificate was used in the above example but do you know if EAP-TLS machine certificate is possible? At my job we use EAP-TLS machine certificates for our computers but we would like to now extend EAP-TLS machine certificates to the Andriods. Also, in the example you launched the http://your-server-ip/certsrv from a computer then exported/imported to the Andriod, is it possible download/install the cert from http://your-server-ip/certsrv directly onto the Andriod or must the export/import step be used?
Hi,
As far as I know it’s only possible to use “user certificates” on the Android devices. Maybe there’s a proprietary solution somewhere but it seems there’s no support. I haven’t seen any SCEP support for Android devices.
I do believe that on Android 4.x devices it is possible to go to http://your-server-ip/certsrv directly and request the certificate right from your Android device. I didn’t try this yet so if you do and it works, please let me know
Rene
Hello,
Do you know if it is possible to backup the certificate storage in the android device? Several of our users manage to factory reset their devices from time to time, and every time we have to generate each certificate and import it again. If we could just backup their certificate storage (and in some cases, even teach them how to do it), we would reduce support requests a lot.